Zyxel USG FLEX Command Injection Vulnerability
The Zyxel USG FLEX Series supports IPsec, SSL, and L2TP-based VPNs, making it an ideal solution for providing a secure network to access remote or home-based workers. Zero-configuration remote access removes complicated setup challenges making it easier for employees to establish VPN connections to the office without the need for IT support.
An OS command injection vulnerability in the CGI program of Zyxel USG FLEX 100(W) firmware could allow an attacker to modify specific files and then execute some OS commands on a vulnerable device.
OS Command Injection
OS command injection (also known as shell injection) is a web security vulnerability that allows an attacker to execute arbitrary operating system (OS) commands on the server that is running an application, and typically fully compromise the application and all its data. Very often, an attacker can leverage an OS command injection vulnerability to compromise other parts of the hosting infrastructure, exploiting trust relationships to pivot the attack to other systems within the organization
Zyxel USG FLEX Command Injection | CVE-2022-30525
An attacker can inject remote commands on the vulnerable Zyxel devices by sending a malicious command containing an mtu field with a crafted OS command to the /ztp/cgi-bin/handler page. This will result in unauthenticated remote command execution as the nobody user.
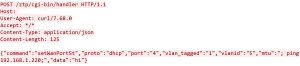
By sending a malicious setWanPortSt command containing an mtu field with a crafted OS command to the /ztp/cgi-bin/handler page, an attacker can gain remote command execution as the nobody user.
Following are the affected versions
- USG FLEX 100(W), 200, 500, 700 ZLD V5.00 through ZLD V5.21
- USG FLEX 50(W) / USG20(W)-VPN ZLD V5.10 through ZLD V5.21
Zyxel has patched this vulnerability.
SonicWall Capture Labs provides protection against this threat via following signatures:
- IPS 15761:Zyxel USG FLEX 100W Command Injection
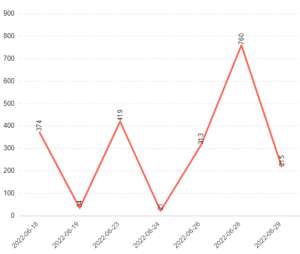
Threat Graph