WordPress WP Statistics plugin SQL Injection
WP-Statistics is an advanced plugin that tracks your website statistics. It analyzes your website’s users by showing their browser, the search engine they use, and the most visited contents based on categories, tags, and authors. The plugin also allows the export of statistical data into different formats. The primary way of communicating with WordPress is over HTTP protocol.
A SQL injection vulnerability exists in WP Statistics Plugin for WordPress. The vulnerability is due to insufficient sanitization of the current_page_id and current_page_type parameter.
Sql Injection
SQL injection attacks occur when SQL commands are injected into data-plane input in order to affect the execution of predefined SQL commands. A SQL injection attack consists of insertion or “injection” of a SQL query via the input data from the client to the application. A successful SQL injection exploit can read sensitive data from the database, modify database data and execute administration operations on the database.
WordPress WP Statistics plugin SQL Injection|CVE-2022-25148
The WP Statistics WordPress plugin is vulnerable to SQL Injection due to insufficient escaping and parameterization of the current_page_id parameter found in the class-wp-statistics-hits.php file . This allows unauthenticated attackers to inject arbitrary SQL queries to obtain sensitive information.
The vulnerable versions are 13.1.5 and up.
Following are some examples of exploits


Vulnerable current_page_id is exploited to make the query sleep for certain time.


Vulnerable current_page_type is exploited to make the query sleep for certain time.


This vulnerability is patched.
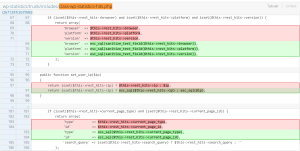
In the patched code we can see that, they are now escaping the input and using parametrized query.
SonicWall Capture Labs provides protection against this threat via following signatures:
- IPS 2553:WordPress WP Statistics plugin SQL Injection 1
- IPS 2554:WordPress WP Statistics plugin SQL Injection 2
- IPS 2567:WordPress WP Statistics plugin SQL Injection 3
Threat graph