VMware vCenter Server vSAN Health Check plug-in RCE Vulnerability
Overview:
Multiple vulnerabilities have been discovered and reported in the VMware vSphere Client (HTML5), specifically in VMware vCenter Server vSAN Health Check plug-in product. Among these vulnerabilities, CVE-2021-21985 is a remote code execution vulnerability rated as Critical.
CVE-2021-21985 is caused by invalid input checking in the Virtual SAN Health Check plug-in which is enabled by default in vCenter Server. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server.
SonicWall’s, (IPS) Intrusion Prevention System, provides protection against this threat:
- IPS: 15574 VMware vCenter Server vSAN Health Check plug-in Possible RCE Attempt 1
- IPS: 15575 VMware vCenter Server vSAN Health Check plug-in Possible RCE Attempt 2
- IPS: 15576 VMware vCenter Server vSAN Health Check plug-in Possible RCE Attempt 3
Note: given that vCenter is likely enabled for access via TLS/HTTPS, DPISSL (Server deployment) would have to be enabled in order for these signatures to cover all cases of a real world exploitation of this vulnerability.
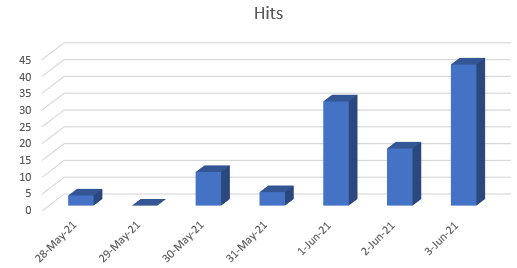
SonicWall has detected the following attacks with the above signatures:
Remediation Details:
The risks posed by this vulnerability can be mitigated or eliminated by:
- Reconfigure the plugin settings according to the vendor advisory.
- Apply the updates from the vendor.
The vendor has released the following advisory regarding this vulnerability:





