SkyStars ransomware, variant of BlackMoon banking trojan encrypts with no recovery note
The SonicWall Capture Labs Threat Research Team observed reports of a variant of the BlackMoon banking trojan called SkyStars. BlackMoon was originally designed to steal user credentials from various South Korean banking institutions. In addition to data theft, the authors later added ransomware capability. This SkyStars ransomware component seems to be in early development.
Infection Cycle:
The Trojan uses the following icon:
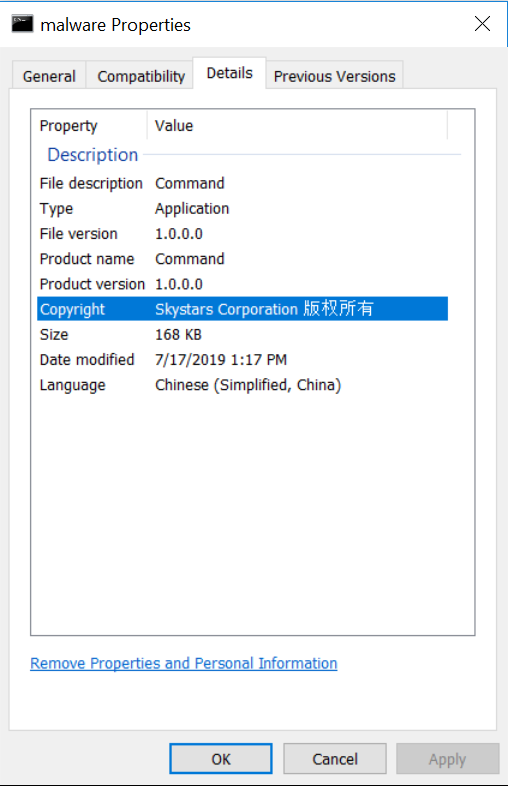
The trojan executable file contains the following metadata:
Upon execution, files are indiscriminentely encrypted on the system. The malware does not appear to have a list of preferred file types. Encrypted files are given a .SKYSTARS extension. The malware does not display a ransom note and no payment method for file recovery is presented to the victim.
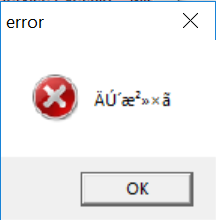
After a period of 5 minutes, the following messagebox is displayed:
Analysis of the executable file reveals the following strings:
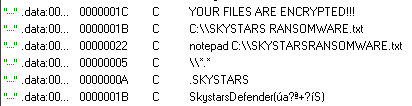
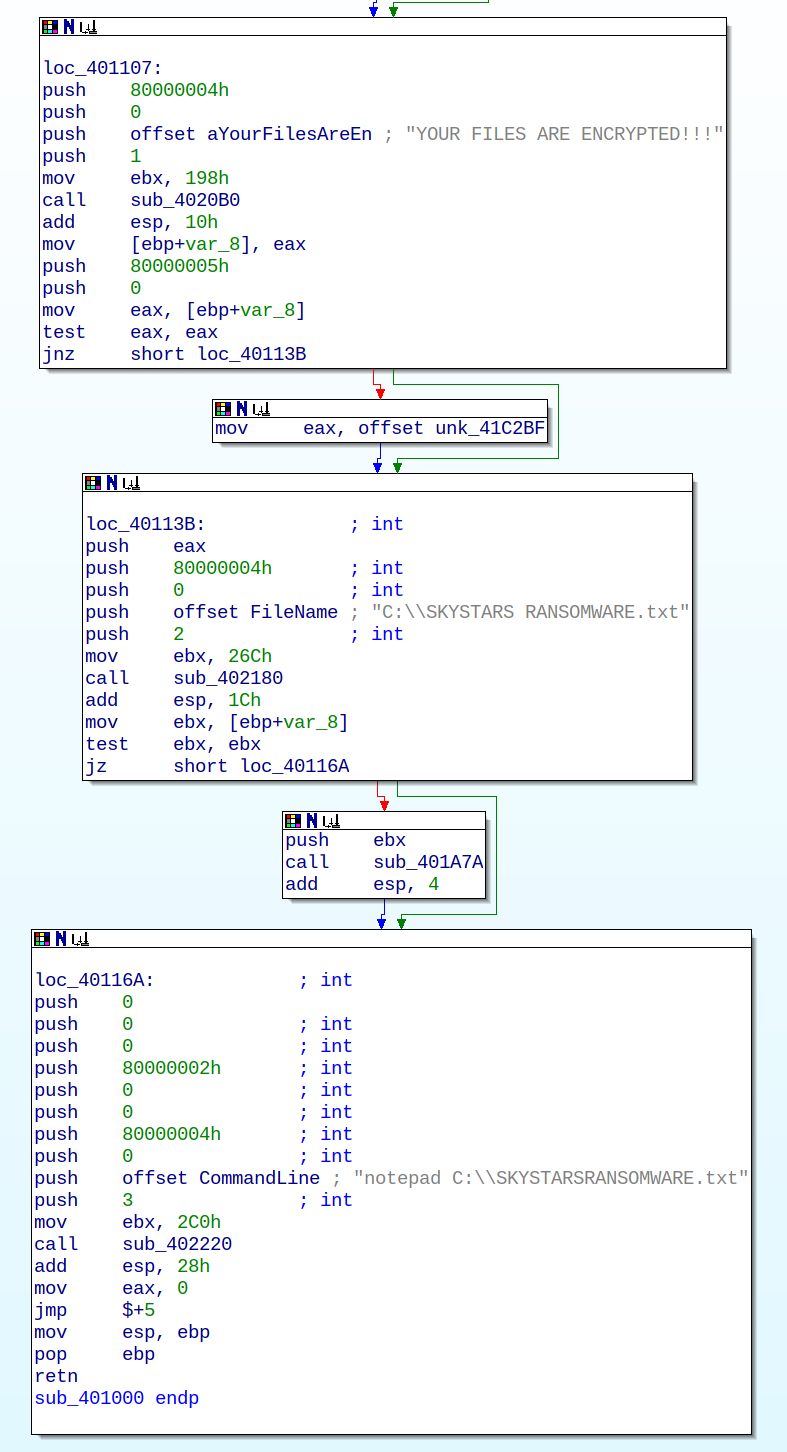
Like most ransomware, the trojan contains functionality to write a ransom note to a file and display it to the victim. Although the code below is present in the malware it was not executed during our analysis:
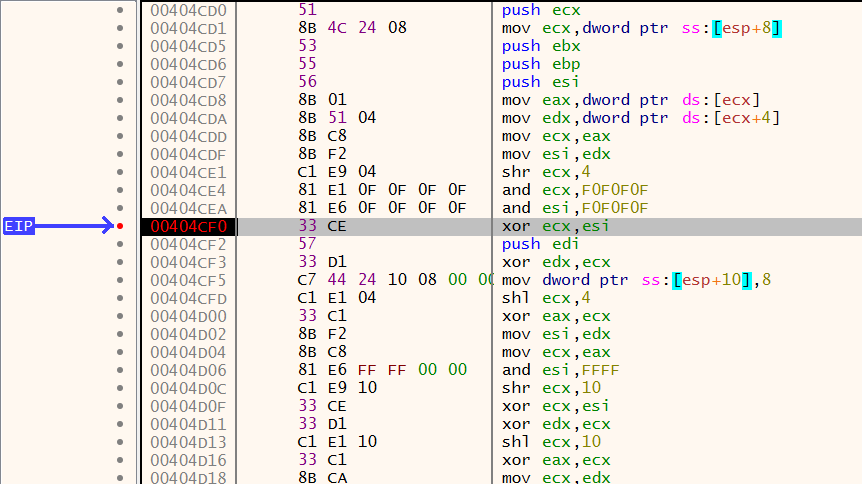
During runtime analysis we were able to locate the encryption function used to encrypt files. The reverse algorithm of this function may be the only possibly way to recover files:
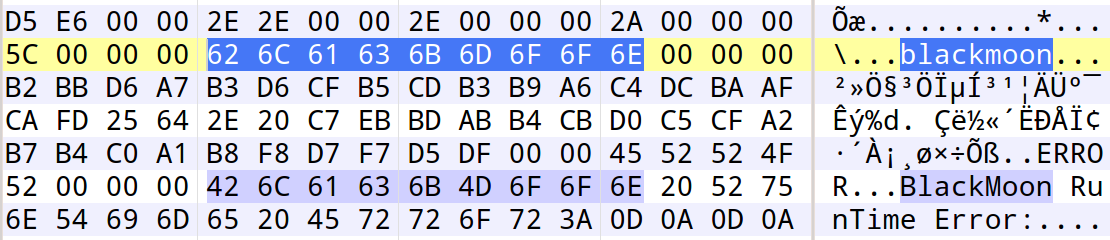
The malware executable file contains strings that refer to BlackMoon, a known banking trojan. This suggests that the malware is a variant of BlackMoon with added ransomware capability:
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: SkyStars.RSM (Trojan)
This threat is also detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.





