March 2021 OpenSSL Vulnerability
Overview:
A denial of service vulnerability has been reported in OpenSSL library. An OpenSSL TLS server may crash if a remote attacker sends a maliciously crafted renegotiation ClientHello message (the exploit) from a client. If a TLSv1.2 renegotiation ClientHello omits the signature_algorithms extension (where it was present in the initial ClientHello), but includes a signature_algorithms_cert extension then a NULL pointer dereference will result, leading to a crash and a denial of service attack. A server is only vulnerable if it has TLSv1.2 and renegotiation enabled (which is the default configuration). OpenSSL TLS clients are not impacted by this issue. All OpenSSL 1.1.1 versions are affected by this issue.
CVE Reference:
This vulnerability has been assigned the Common Vulnerabilities and Exposures (CVE) identifier CVE-2021-3449,
dated 2021-03-17.
Common Vulnerability Scoring System (CVSS):
The overall CVSS score is 6.5 (CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C).
Base score is 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H), based on the following metrics:
• Attack vector is network.
• Attack complexity is low.
• Privileges required is none.
• User interaction is none.
• Scope is unchanged.
• Impact of this vulnerability on data confidentiality is none.
• Impact of this vulnerability on data integrity is none.
• Impact of this vulnerability on data availability is high.
Temporal score is 6.5 (E:U/RL:O/RC:C), based on the following metrics:
• The exploit code maturity level of this vulnerability is unproven.
• The remediation level of this vulnerability is official fix.
• The report confidence level of this vulnerability is confirmed.
Technical Overview:
The primary goal of the SSL protocol, Secure Socket Layer (SSL) is to provide privacy and reliability between two communicating applications and the primary goal of the TLS protocol, Transport Layer Security (TLS) is to provide a secure channel between two communicating peers. Both protocols are cryptographic protocols that provide authentication, confidentiality and data integrity for communication over TCP/IP networks. By using cryptographic algorithms such as symmetric key ciphers, cryptographically secure hash functions, and asymmetric cryptography, also known as public-key cryptography, is a process that uses a pair of related keys; one public key and one private key; to encrypt and decrypt a message and protect it from unauthorized access or use. The listed protocols enable hosts to communicate securely over insecure networks.
Triggering the Problem:
• The target must have a vulnerable version of the product running, with TLS 1.2 enabled.
• The target application must have TSL renegotiation enabled.
• The attacker must have network connectivity to the vulnerable application.
Triggering Conditions:
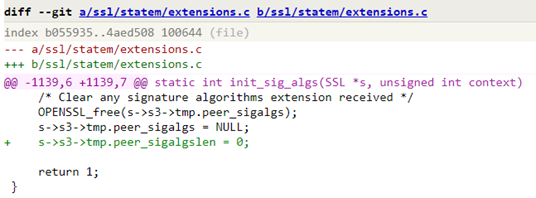
The attacker sends a TLS 1.2 Client Hello handshake message containing a non-empty signature_algorithms extension, then renegotiates with an empty signature_algorithms extension but non-empty signature_algorithms_cert extension. The vulnerability is triggered when the server processes the new Client Hello message.
Attack Delivery:
The following application protocols can be used to deliver an attack that exploits this vulnerability:
• TLS
• HTTPS, over ports 443/TCP, 8443/TCP
• SMTP, over ports 25/TCP, 587/TCP
Patched Software:
SonicWall’s, (IPS) Intrusion Prevention System, provides protection against this threat:
• IPS: 15483 “Client Renegotiation within Short Period”
Remediation Details:
The risks posed by this vulnerability can be mitigated or eliminated by:
• Upgrading to the patched releases to eliminate the vulnerability.
• Disabling TLS 1.2 version in OpenSSL.
• Disabling renegotiation if it was not needed.
The vendor has released the following advisory regarding this vulnerability:
Open SSL News Advisory
Appendix – Discovered By:
This issue was reported to OpenSSL on 18th March 2021 by Benjamin Kaduk from Akamai and was discovered by Xiang Ding and others at Akamai. The fix was developed by Tomáš Mráz.