Lokibot Malware exploits spotted in the wild
SonicWall Capture Labs Threats Research Team has spotted Lokibot malware attacks in the wild. This malware is delivered through spam emails . Lokibot is an info stealer and tries to steal credentials stored in registry, files and browser.
It also reads sensitive data of Google chrome, Firefox, Internet Explorer. It tries to connect to attacker controller server over HTTP and tries to POST the stolen information from the victim’s computer.
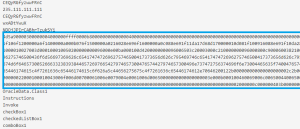
Infection Cycle
User is lured into opening malicious attachment in spam email. This attachment is lokibot malware which upon execution steals sensitive user data like username password in browser and registry.
This malware shows following behavior :
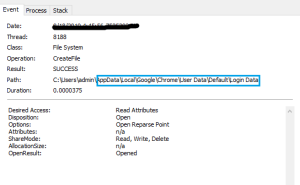
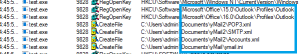
- Tries to read sensitive data of: LinasFTP, Mozilla Firefox, Google Chrome, QtWeb Internet Browser, Internet Explorer / Edge.
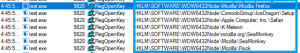
- Reads installed programs by enumerating the SOFTWARE registry key.
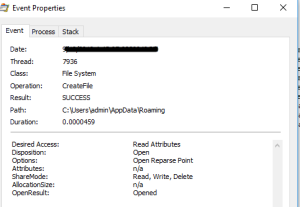
- Trying to read sensitive data of web browsers like Firefox, Google Chrome, Internet Explorer
- Trying to read sensitive data from ftp applications through registry like LinsaFTP
- Trying to read sensitive email data from Microsoft Outlook
![]()
![]()
![]()
![]()
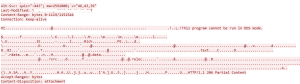
The malware sends the information to attacker-controlled server [185.250.240.84]
![]()
The malware has embedded executable stored as hex formatted string.
It also downloads file from hxxp://185.250.240.84/xxxx/[filename].exe
Sonicwall Capture Labs provides protection against this threat with the following signature:
- Lokibot.XS
- Lokibot.XS_2
- LokiMD
- LokiBot.DN
- Lokibot.SI
This threat is also detected by SonicWALL Capture ATP w/RTDMI
IoCs
b94f1e79967593212bcc4d87d7cb1126c7058b29c5e72192be4c723333c50827
1c60762ed20269d0e92549ab12fe71dfcf014187339457c84a6d0bf6cea17c8f
691c65e4fb1d19f82465df1d34ad51aaeceba14a78167262dc7b2840a6a6aa87
4aba53fe8e5e914bd4ce329202ab254e0e428851c8fda399a0cc64b848cee165
2e0803bf1552657d7cf082bb1fd8b605cea4b8734639f18b127d619341e960a0
03bb2466c3be7ac4fd3e8b970731ab5627da89b0653dc9449e7faddddb643934




