Large scan activity observed for Digital Video Recorder NVMS-9000
SonicWall Capture Labs Threat Research Team observed large unusual scan activity looking for DVR NVMS-9000-series no-name type network-attached devices.
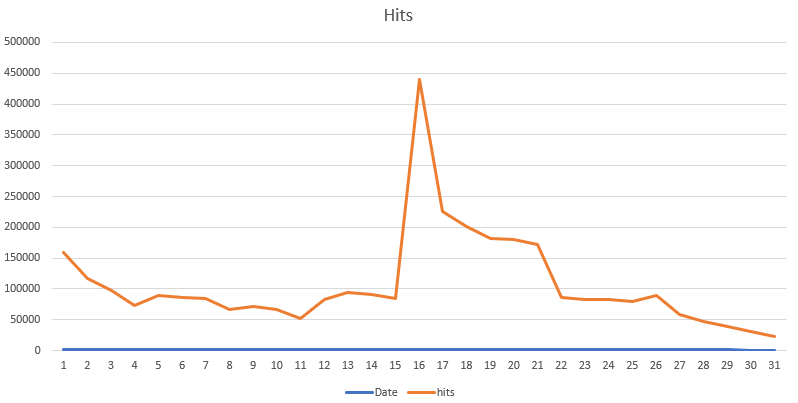
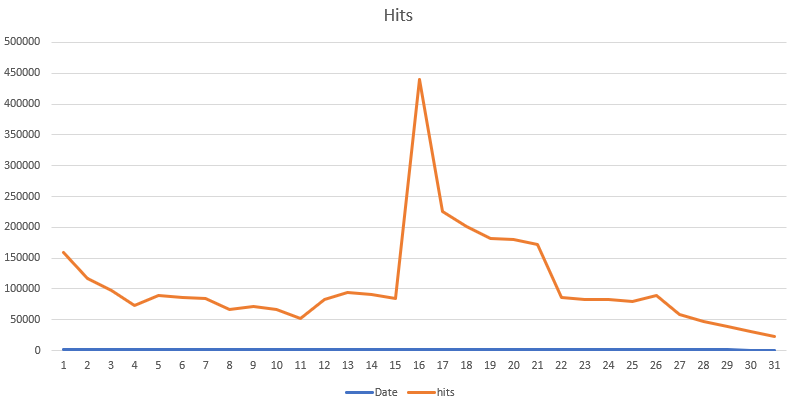
Fig: Hits for the IPS signature 14610 in the last 30 days
The traffic with the shellcode is given below. It uses the hardcoded username\ password to authenticate and attempts to fork a reverse shell to redirect the traffic to a remote listener on port TCP 31337.
Fix:
The vendor advisory is posted here where they recommend updating the firmware.
If you have NVMS-9000 DVR exposed to the web, check for any unusual activity and block all inbound access from the web.
SonicWALL Capture Labs Threat Research team provides protection against this threat with the following signature:
IPS: 14610 NVMS-9000 Digital Video Recorder Remote Code Execution



