GULoader
Overview:
SonicWall Capture Labs Threat Research Team recently found a new sample and activity in April for a downloader called GuLoader. GuLoader is used in conjunction with other malware components such as RATs (Remote Administration Tools). Some of the well-known components for 2020 are: Parallax, Netwire, FormBook, Tesla RATs.
The binary is compiled with Visual Basic 5.0/6.0. Visual Basic is somewhat cryptic to read and understand while using many of the reverse engineering tools such as Disassemblers, Decompilers, and Hex Editors. Most of the Visual Basic programmers are from the early 90’s. Which probably means the malware author is older, Most likely in his/her late 30’s or 40’s.
This binary is used in conjunction with Initial Access components such as Spearphishing applied as an email attachment. Most of the email attachments will be compressed such as zip or rar files.
The loader is protected with an xor encryption, the encryption uses a 4-byte key to unpack its executable stub. The binary is also armored with Anti-Debugging techniques such as NtSetInformationThread and custom ExceptionHandlers to watch for single stepping or toggled breakpoints.
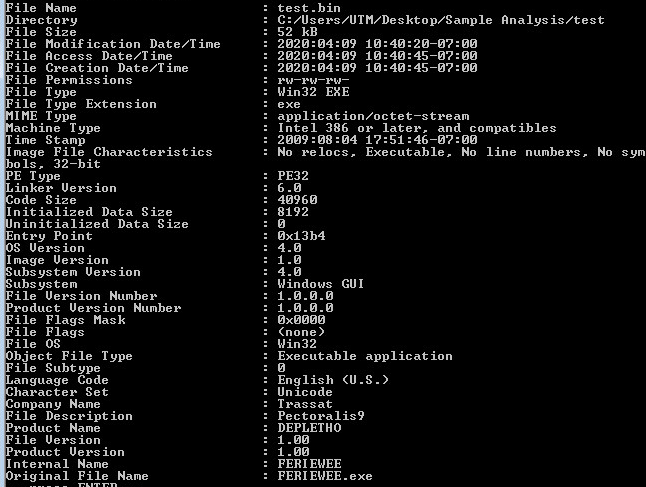
Samples: 1st Layer, Static Information:
Looking at the first layer in CFF Explorer, checking for corruption. The first layer is a Visual Basic 5.0 Win32 binary.
Command-line static information:
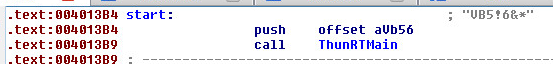
Main starting routine from IdaPro:
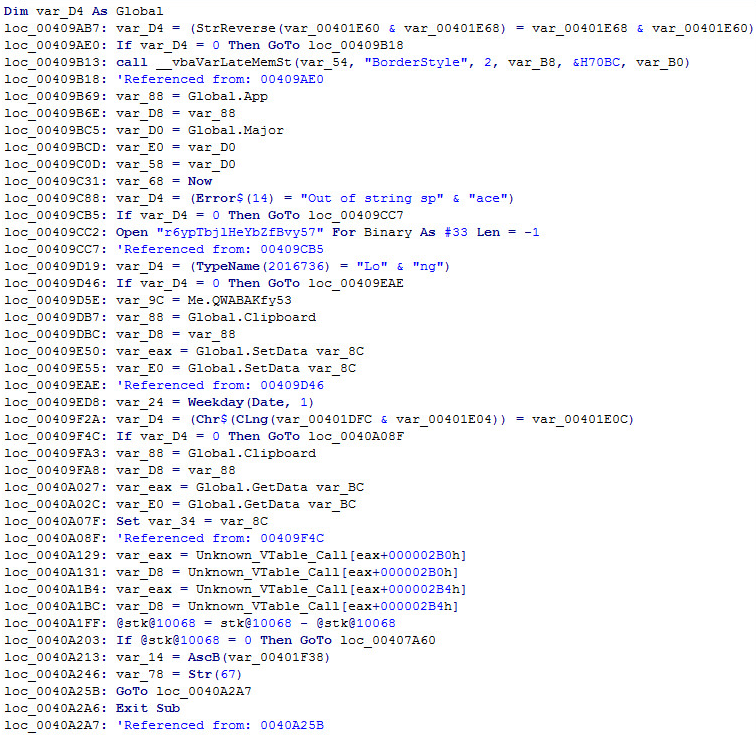
Main starting routine in VB Decompiler:
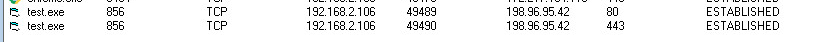
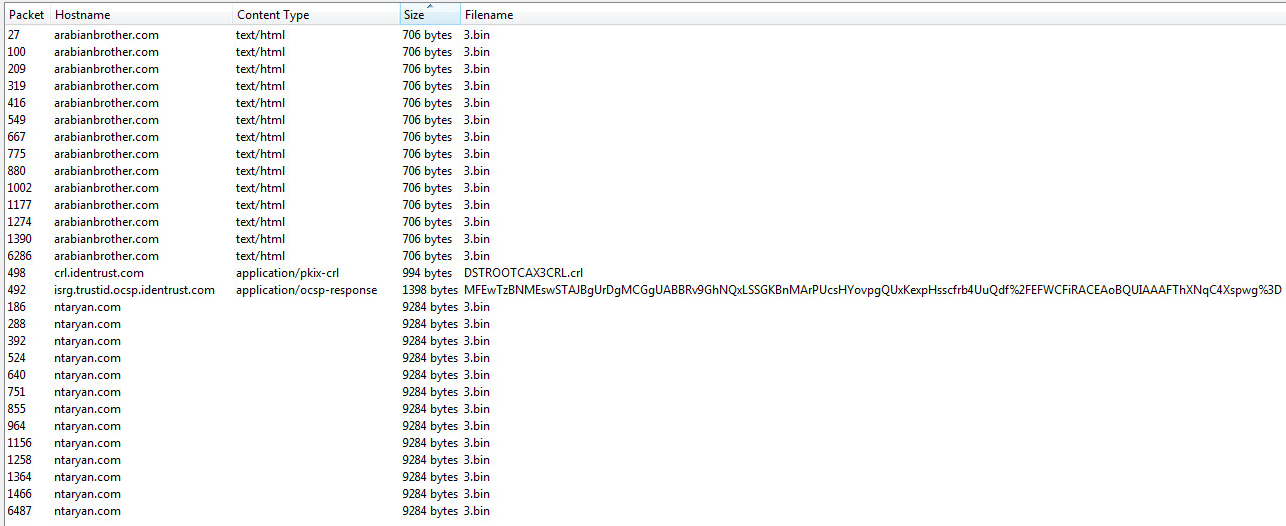
HTTP Network Connections & Objects:
Connections:
Objects:
The binary will reach out and grab an exe called “3.bin” from multiple domains:
- arabianbrother.com
- ntaryan.com
Supported Systems:
- Windows 10
- Windows 8.1
- Windows 8.0
- Windows 7
- Windows Vista
SonicWall, (GAV) Gateway Anti-Virus, provides protection against this threat:
- GAV: GULoader.PN
Appendix:
Sample Hash: 1b1279f4eca61a6661eb687cba8566b20fdc0cfa17bed09a6c0b87d53e7055dd