Data stealing trojan posing as a PDF document (June 5, 2015)
The Dell SonicWall Threats Research team has received reports of a data stealing Trojan posing as a PDF document. Upon execution, the trojan downloads more malware onto the infected machine and also steals information from the system.
Infection Cycle:
The Trojan uses the following icon:
Figure 1: Trojan purports to be a PDF document
![]()
Upon looking at the properties, the trojan is described in Norwegian as “flash game KLP – pension, banking and insurance to municipalities, health authorities, businesses and their employees.”

Upon execution, Adobe throws the following error:

The Trojan creates a copy of itself in the following location:
- %Application Data%sample.exe [Detected as GAV: Downloader.FAUT (Trojan)]
In order to start after reboot the malware makes a copy of itself in the following location:
- %%USER%softwaremicrosoftwindowscurrentversionrun[b528c54d1cfbb1b9bc2e8ffca007591][Detected as GAV: Downloader.FAUT (Trojan)]
The trojan injects into the following processes:
- C:WINDOWSexplorer.exe
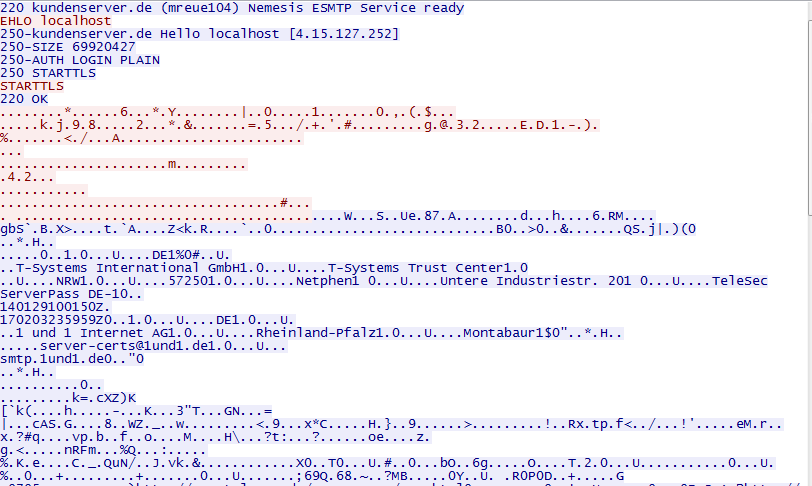
It tries to connect to the following domains:
- mbaexecutiveranking.com
- ekonomik-komerc.co.rs
- gouliami.gr
- smtpmail.t-online.de
- smtp.1und1.de
- smtp.mail.yahoo.com
- mail.tel.net.ba
It periodically sends encrypted data to the remote C&C servers:


It downloads additional malware onto the victim’s machine, detected as GAV: Fiha.A_26 (Trojan)

The malware starts sending spams to the email addresses retrieved from its C&C server, here an example:
Overall, this Trojan is capable of downloading additional malware into the victim’s machine. It can also send sensitive information out to a remote server.We urge our users to always be vigilant and cautious with any unsolicited attachments specially if you are not certain of the source.
Dell SonicWALL Gateway AntiVirus and Intrusion Prevention provides protection against this threat with the following signatures:
- GAV:Downloader.FAUT (Trojan)
- GAV:Fiha.A_26 (Trojan)




