CODESYS web server buffer overflow CVE-2019-18858
CODESYS
CODESYS is a development environment for programming controller applications.
CODESYS WebVisu
The CODESYS web server is used by the CODESYS WebVisu to display CODESYS visualization screens in a web browser. With a controller, equipped with the CODESYS WebVisu you can comfortably visualize your CODESYS screens optimized in a web browser, whenever and wherever you want.
The Vulnerability
CODESYS 3 web server before 3.5.15.20, as distributed with CODESYS Control runtime systems, has a Buffer Overflow. (CVE-2019-18858)
A buffer overflow condition exists when a program attempts to put more data in a buffer than it can hold or when a program attempts to put data in a memory area past a buffer. Writing outside the bounds of a block of allocated memory can corrupt data, crash the program, or cause the execution of malicious code.
Specially crafted requests to the CODESYS WebVisu server can lead to heap buffer overflow. Further this could crash the web server, lead to a denial-of-service condition or may be utilized for remote code execution. As the web server is part of the CODESYS runtime system, this may result in unforeseen behavior of the complete runtime system.
A remote, unauthenticated attacker can exploit this vulnerability by sending a crafted HTTP request to the target web server. Successful exploitation results in arbitrary code execution in the security context of the process.
Like in the case below, the remote attacker can POST to the WebVsuV3 url containing a special header followed by a long payload(which can be malicious).
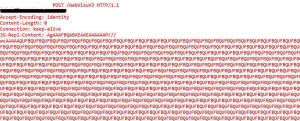
The PoC is publically available here https://github.com/tenable/poc/blob/master/codesys/codesys_v3_webserver_heap_overflow.py
Mitigation
Upgrading the CODESYS 3 web server to version higher than 3.5.15.20 will mitigate the risk .
SonicWALL Capture Labs Threat Research team provides protection against this threat via following signatures:
IPS 14673 CoDeSys CmpWebServer Buffer Overflow 2
IPS 14674 CoDeSys CmpWebServer Buffer Overflow 3




