Caddywiper hits Ukrainian networks. Wipes data and renders machines unbootable
As the war between Russia and Ukraine rages on, the conflict has extended into the cyber domain. In mid-February, the Security Service of Ukraine reported that the country was the target of an ongoing “wave of hybrid warfare” initiated by Russian malicious actors. Caddywiper is one of at least three wiper malware families reported to have been detected on Ukrainian systems. Unlike ransomware, which encrypts files and demands payment for file recovery, this malware indiscriminately wipes anything it can on the system as fast as possible and renders it unusable.
Infection Cycle:
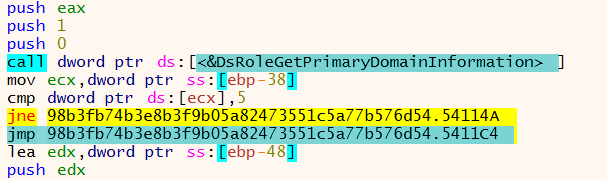
The malware uses DsRoleGetPrimaryDomainInformation to check if the infected machine is a domain controller. If it is, the malware exits without modifying the system. Having this check enables the attackers to continue perusing the network in order to infect more machines:
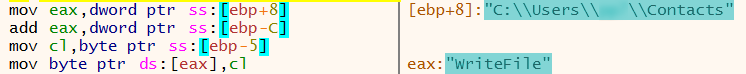
During the wiper process, the malware is seen iterating through files on the system and replacing its contents with null bytes:
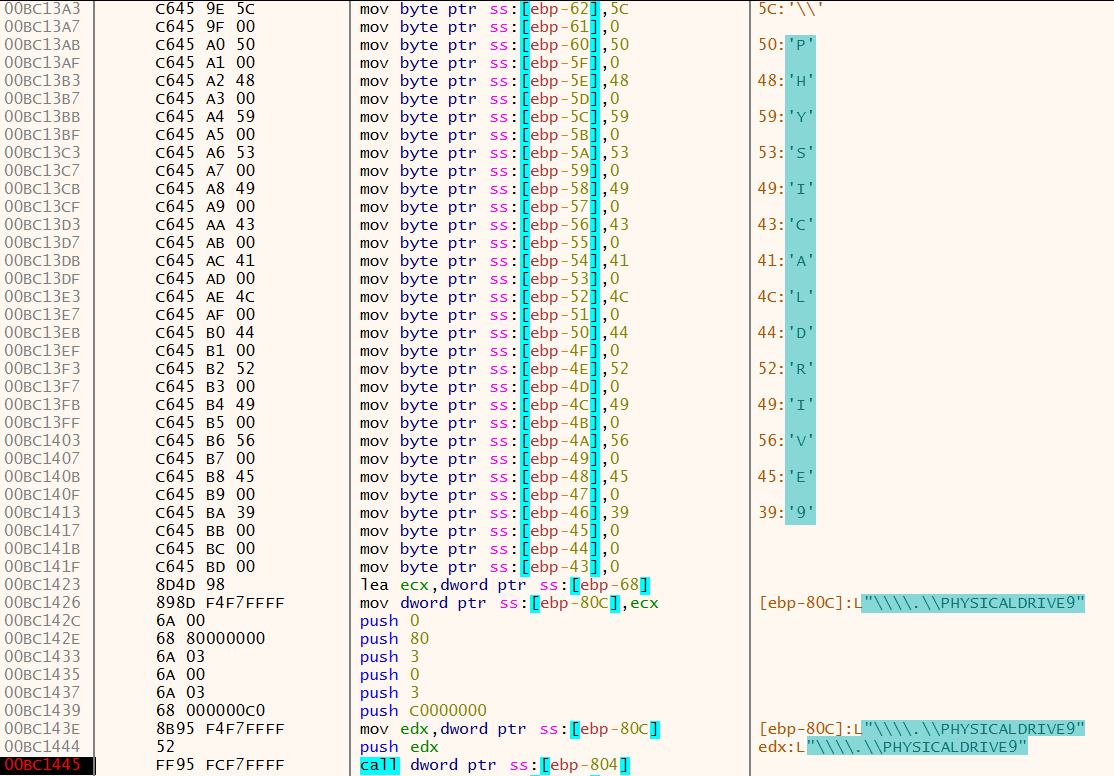
The physical drive is the final target and is overwritten with null bytes. This renders the machine unbootable:
Critical system files are overwritten during the wiper process. When this happens, it causes the machine to immediately shutdown and provide a shell prompt:
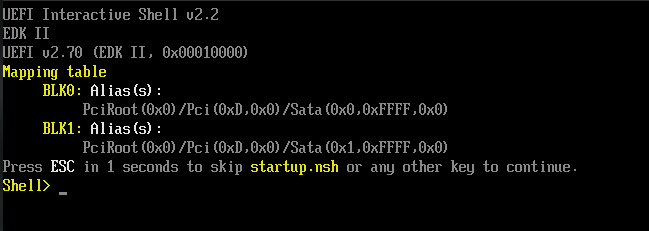
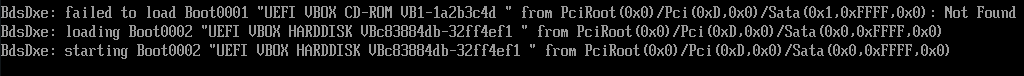
After reboot, the following message is displayed during the boot process. The system is unable to boot:
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: Caddywiper.A (Trojan)
This threat is also detected by SonicWall Capture ATP w/RTDMI and the Capture Client endpoint solutions.





