Adobe Flash Player memory corruption vulnerability CVE-2017-2930 (Jan 20, 2017)
A memory corruption vulnerability exists in Adobe Flash Player versions 24.0.0.186 and earlier. An attacker can lure the victim into opening specially crafted malformed flash file.
This vulnerability will allow the remote attacker to run malicious code in context of the current user.
CVE-2017-2930 can be triggered by a swf file with an ActionRecord structure that contains an invalid value in ActionGetURL2.
The flash player crashes when the swf is opened.
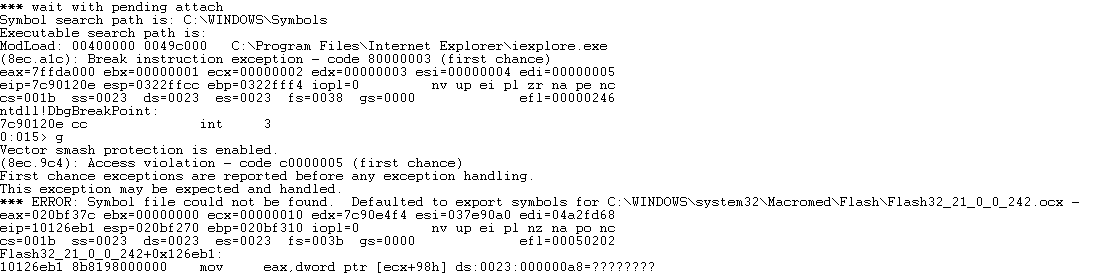


The flash file tries to open an invalid address multiple times, which creates many instances of IE causing a Denial of Service (DoS) and the machine to become unresponsive.


The PoC can be found here.
Adobe has patched this vulnerability in the Jan 2017 patch Tuesday.
SonicWALL Threat Research Team has researched this vulnerability and released following signature to protect their customers.
- SPY 1274 : Malformed-File swf.MP.525_2





