Ada_Covid ransomware operator uses WhatsApp for price negotiation
The SonicWall Capture Labs threat research team have come across a new ransomware family known as Ada Covid. The sample we analysed appears to be in early stages of development and does not modify any files on the system. It does, however, contain the ability to do so. An interesting shift with this malware is that the operators have chosen WhatsApp as a means of communication with infected users. This could be in response to the social change triggered by the current global pandemic. The operators perhaps, realize that instant messaging is a more effective negotiation medium when victims are stuck at home abiding by shelter-in-place orders. This is opposed to messaging via email, the medium of choice for many ransomware operators in the past.
Infection Cycle:
The malware is reported to have been served via the following link which is no longer active:
https://www.ktalents.com.my/wp-admin/images/Covid-19%20Check.exe
The trojan executable file uses the following icon:
The executable file is an sfx archive that contains 3 files:
- fud.bat
- server.exe
- server.sfx.exe
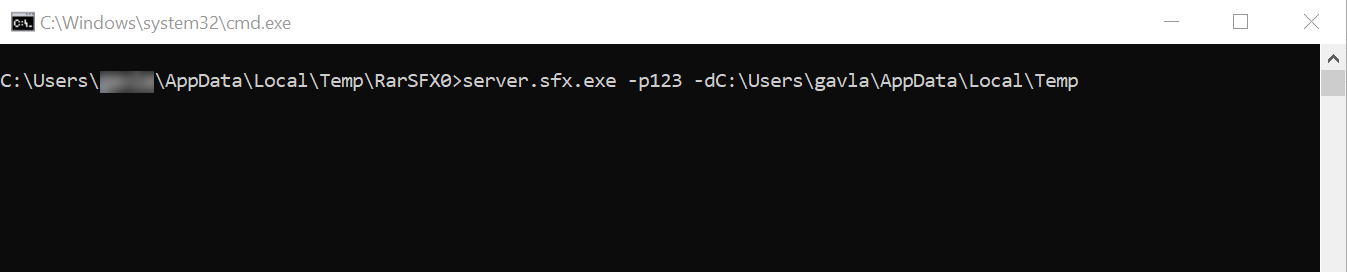
fud.bat contains the following script:
server.sfx.exe -p123 -d%temp%
Upon running the executable, the following command line box appears while extracting files from the sfx archive:
The following files are added to the system:
- %USERPROFILE%\AppData\Local\Temp\RarSFX1\server.exe [Detected as: GAV: Ada_Covid.RSM (Trojan) ]
- %USERPROFILE%\AppData\Roaming\Microsoft\Windows\Recent\Name of your explain.lnk
- %USERPROFILE%\OneDrive\Desktop\Name of your explain.txt
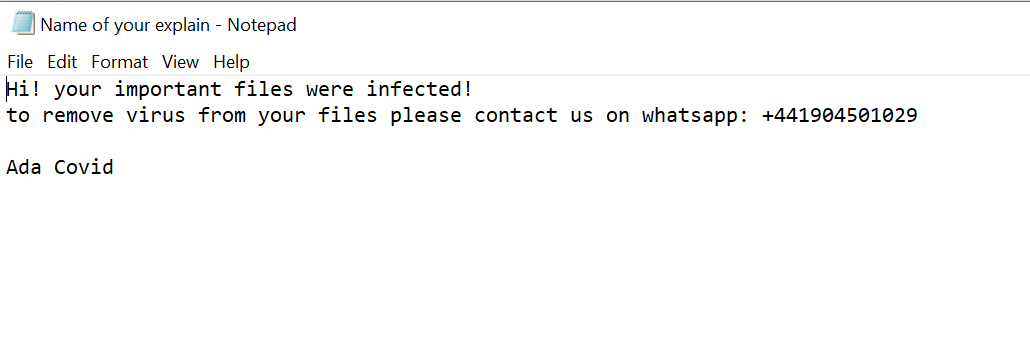
The following message is displayed on the desktop in notepad:
The malware is written in .NET and is easy to decompile. Although no modification of files took place during our analysis, the code evidently contains functionality to encrypt files. It is coded to give encrypted files a .pdf extension:
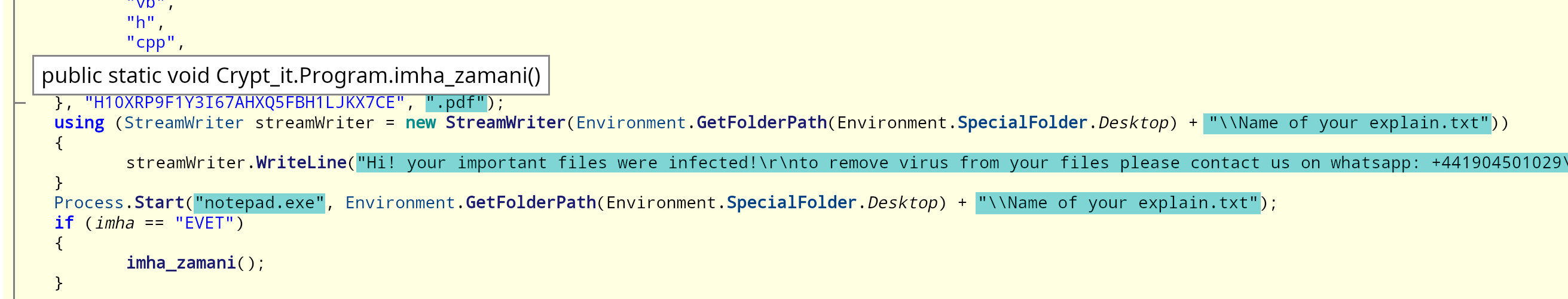
If files were actually encrypted, the encryption key (1,2,3,4,5,6,7,8) is easy to obtain:
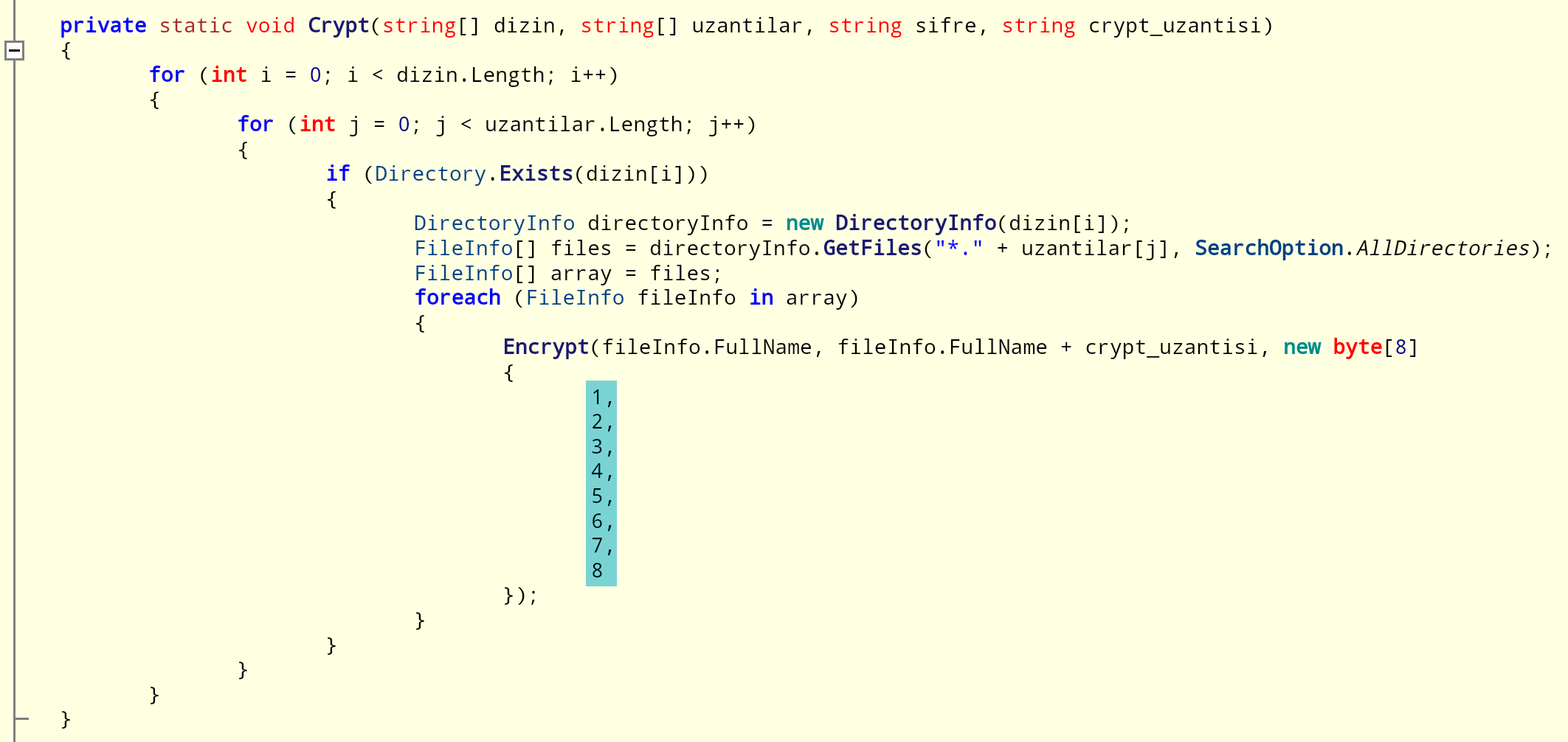
Decompilation of the encryption function shows a list of file types to target:
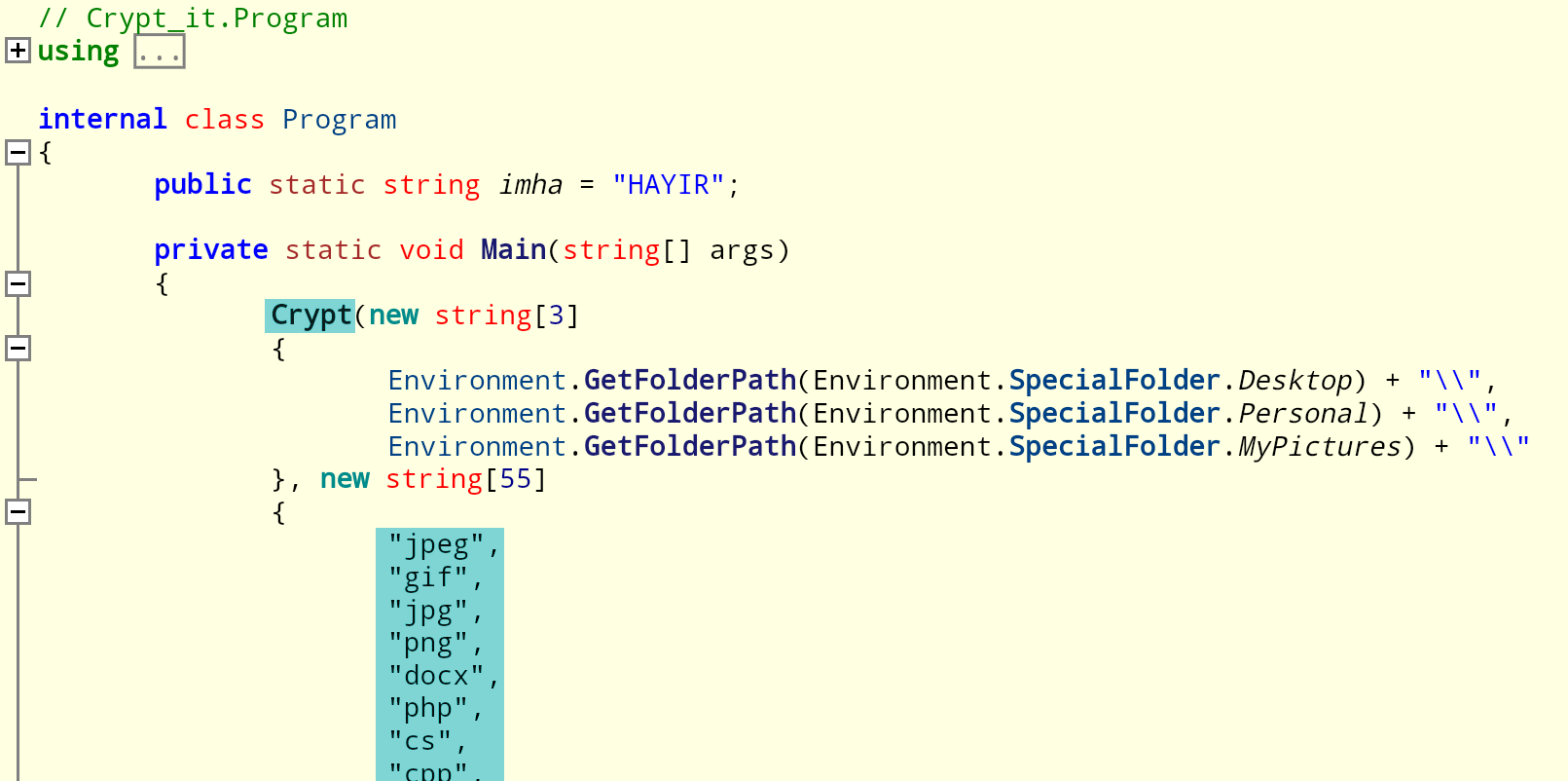
The following file types are targeted:
jpeg, gif, jpg, png, docx, php, cs, cpp, rar, zip, html, htm, xlsx, avi, mp4, xls, pdf, odt, ods, pptx, ppt, doc, jpej, mid, midi, mp3, wav, bat, psd, psp, tif, iso, mdb, sql, log, dat, csv, com, cgi, py, aspx, cer, css, htm, part, c, class, java, sh, swift, vb, h, cpp, bak, wpd
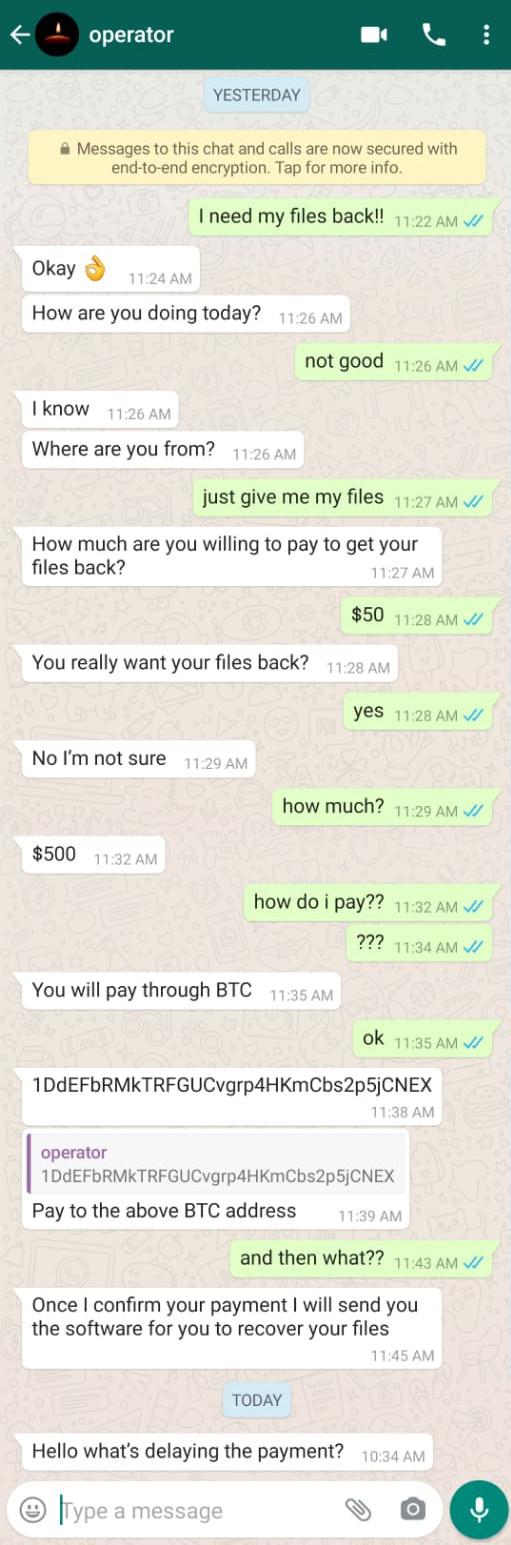
As stated in the ransom message, WhatsApp is the medium of choice for negotiation. We had the following conversation with the operator via WhatsApp:
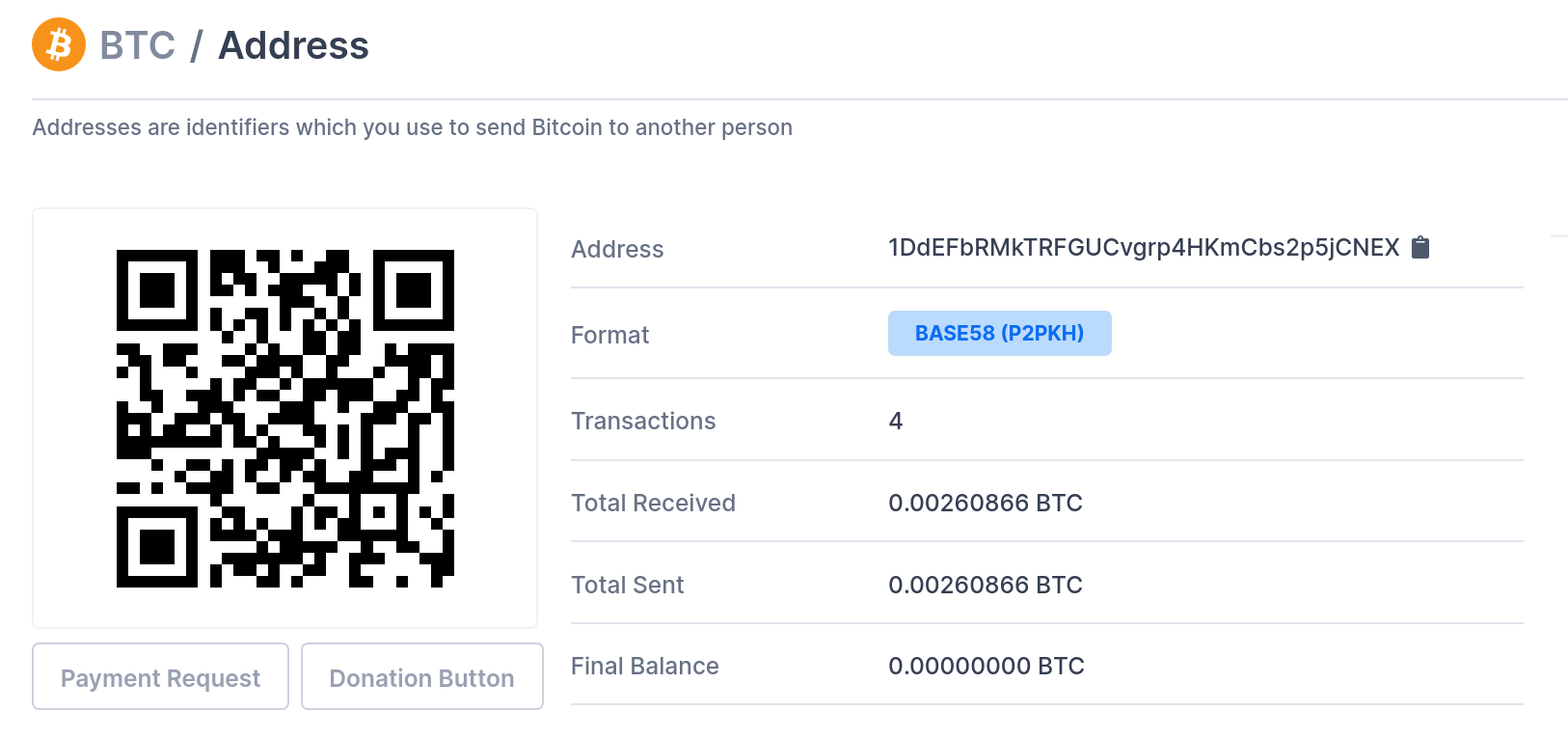
There has been some transaction activity at the supplied address. However, this does not necessarily indicate success:
SonicWall Capture Labs provides protection against this threat via the following signature:
- GAV: AdaCovid.RSM (Trojan)
This threat is also detected by SonicWALL Capture ATP w/RTDMI and the Capture Client endpoint solutions.




